סיכום קצר: הטרנספורמציה הדיגיטלית של שירות הבריאות הלאומי (NHS) מייצגת מעבר מקיף ממתכונת אנלוגית למתכונת דיגיטלית במתן שירותי בריאות, המונע על ידי "תוכנית הבריאות העשירית" של הממשלה. עם למעלה מ-28 מיליון משתמשים באפליקציית ה-NHS, השקעה של 150 מיליון ליש"ט בדיגיטליזציה של שירותי הרווחה, ומנדט לשיפור הפריון השנתי בשיעור של 2%, ה-NHS עובר מודרניזציה באמצעות רשומות רפואיות אלקטרוניות, מערכות מקושרות וכלים מבוססי בינה מלאכותית, במטרה להשיג תוצאות טובות יותר עבור המטופלים וערך מוסף עבור משלמי המסים.
שירות הבריאות הלאומי (NHS) עובר את השינוי הטכנולוגי המשמעותי ביותר זה עשרות שנים. ממערכות מיושנות המבוססות על נייר לתשתית דיגיטלית מקושרת, השינוי הזה אינו נוגע רק לטכנולוגיה — הוא נוגע לחשיבה מחודשת מהיסוד על האופן שבו ניתנים שירותי הבריאות ברחבי אנגליה.
לפי נתוני ה-NHS באנגליה, כיום יש ליותר מ-40 מיליון אנשים חשבון ב-NHS, ורוב מוסדות ה-NHS יישמו מערכות לניהול רשומות רפואיות אלקטרוניות. הדבר מייצג שינוי עצום באופן שבו מטופלים מקבלים טיפול ובאופן שבו רופאים מקבלים החלטות קריטיות.
אך כאן טמון האתגר: תוצאות הטרנספורמציה הדיגיטלית ב-NHS היו עד כה דלות. משרד הביקורת הלאומי דיווח כי תוכניות לאומיות מרכזיות קודמות הופסקו בטרם עת מבלי שהשיגו את יעדיהן. כיום, מימון לאומי בסך 4.7 מיליארד ליש"ט משמש להקמת שירותים דיגיטליים לאומיים ולשיפור הבשלות הדיגיטלית בכל רחבי המערכת.
הבנת אסטרטגיית הטרנספורמציה הדיגיטלית של ה-NHS
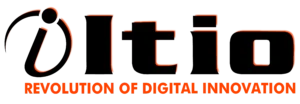
תוכנית הבריאות העשירית לאנגליה, שפורסמה ב-3 ביולי 2025, מתארת שלושה שינויים מהותיים המגדירים את העתיד הדיגיטלי של שירות הבריאות הלאומי (NHS). לא מדובר בשינויים הדרגתיים, אלא בשינויים מבניים שנועדו לתת מענה לעשרות שנים של השקעה חסרה ופיצול.
השינוי הראשון מעביר את הטיפול מבתי החולים לקהילה, כך שיותר שירותים יהיו זמינים בסביבת מגוריהם של האנשים ובבתיהם. כלים דיגיטליים מאפשרים זאת באמצעות חיבור בין שירותי הבריאות הקהילתיים למערכות בתי החולים, מה שמאפשר תיאום חלק בין מסגרות הטיפול השונות.
המהפך השני — מהשיטה האנלוגית לדיגיטלית — משחרר את הצוות מעומס ניהולי ומאפשר למטופלים לנהל את הטיפול הרפואי שלהם בקלות, ממש כמו בבנקאות מקוונת. משמעות הדבר היא תיקי מטופלים אלקטרוניים משולבים, הזמנת תורים באופן דיגיטלי וגישה לתוצאות בדיקות בזמן אמת.
השינוי השלישי מתמקד במניעה ולא בטיפול, תוך שימוש בנתונים ובניתוחים כדי לזהות סיכונים בריאותיים בטרם יהפכו למשברים. הטרנספורמציה הדיגיטלית מאפשרת זאת באמצעות איסוף, אחסון וניתוח של נתונים קליניים ממגוון נקודות מגע.
תיקים רפואיים אלקטרוניים: הבסיס
מערכות התיקים הרפואיים האלקטרוניים (EPR) מהוות את עמוד התווך של המהפכה הדיגיטלית בשירות הבריאות הלאומי (NHS). לא מדובר רק בתיקים מנייר שעברו דיגיטציה, אלא בפלטפורמות מקיפות המשלבות היסטוריה רפואית, תוצאות בדיקות, תרופות ותוכניות טיפול במערכת אחת נגישה.
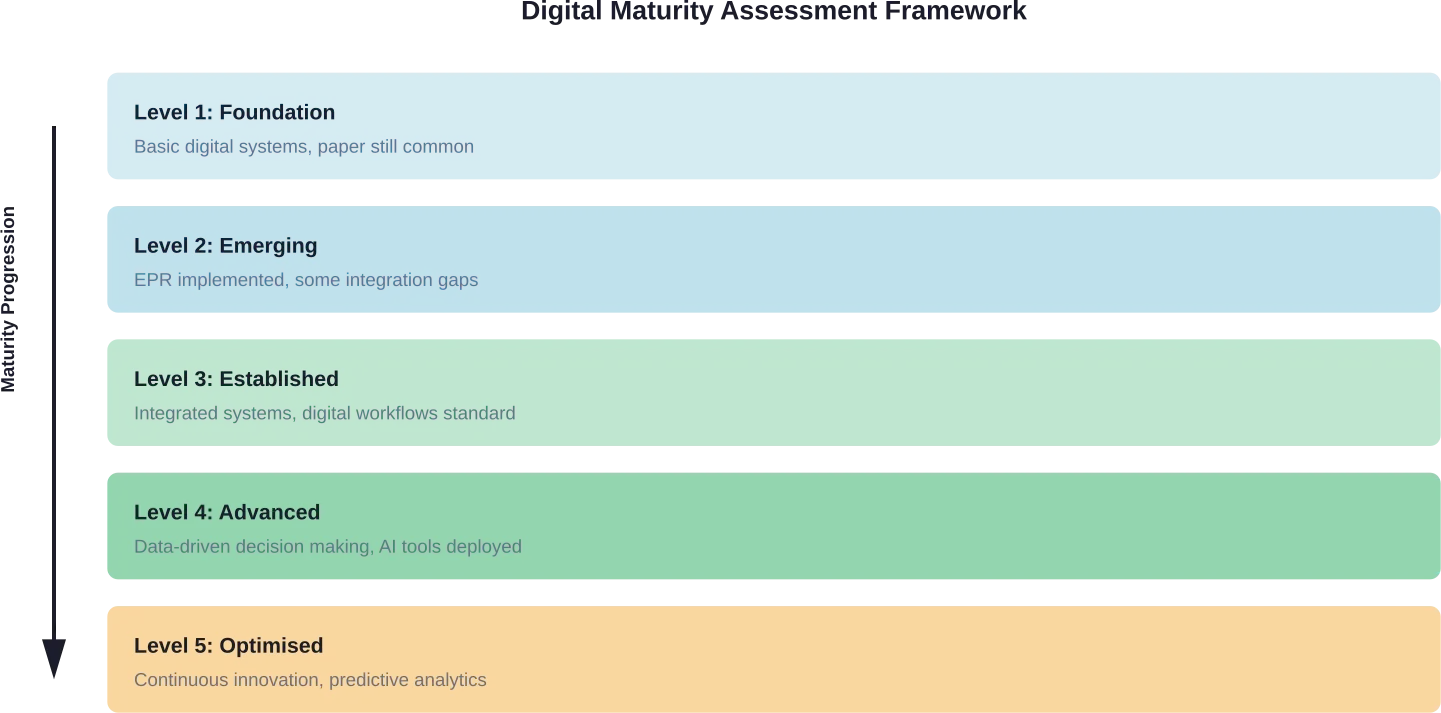
כיום, לרוב קרנות ה-NHS יש מערכות EPR, אך איכות היישום משתנה במידה ניכרת. ‘בגרות דיגיטלית’ מתייחסת ליכולתו של ארגון להגיב לשינויים ולמגמות טכנולוגיות, וניתן לראות בה "מצב של מוכנות" להסתגל ולשלב מערכות חדשות.
ארגון בעל בשלות דיגיטלית מפגין קשר ברור בין האסטרטגיות הדיגיטליות לבין יעדי הליבה העסקיים. לא מדובר רק בקיומה של הטכנולוגיה, אלא בשימוש יעיל בה כדי לשפר את תוצאות הטיפול בחולים ואת היעילות התפעולית.
חברת Proact IT UK Limited מציעה שירותי יישום וטרנספורמציה בתחום ה-ERP והיכולות הדיגיטליות, שנועדו ללוות ארגונים החל מהזיהוי הראשוני של הצורך ועד ליישום מוצלח והעלאת המערכת לאוויר. הגישה שלה כוללת הערכת מוכנות לשינוי, הובלת תוכניות ושירותי תמיכה שוטפים.
אפליקציית ה-NHS ומהפכת הגישה למטופלים
אפליקציית ה-NHS מהווה אולי את ההיבט הבולט ביותר של המהפכה הדיגיטלית עבור המטופלים. עם למעלה מ-28 מיליון משתמשים, היא הפכה לנקודת הגישה העיקרית לשירותי בריאות ברחבי אנגליה.
באמצעות האפליקציה, המטופלים יכולים לקבוע תורים, להזמין מרשמים חוזרים, לצפות בתוצאות בדיקות ולגשת לתיקים הרפואיים שלהם. מעבר זה לניהול עצמי של המטופלים מקל על העומס הניהולי המוטל על הצוות, ובמקביל מעניק לאנשים שליטה על תהליך הטיפול הרפואי שלהם.
אבל האפליקציה היא יותר מסתם נוחות — המטרה היא לאפשר לאנשים לקבל טיפול במהירות ובקלות, בכל זמן שנוח להם. החל מאתרי אינטרנט ואפליקציות שמקלים על הגישה לטיפול בכל מקום שבו נמצאים המטופלים, ועד למערכות מחשב משולבות המספקות לצוות את המידע הדרוש לו, ה-NHS פועל בצורה חכמה יותר כדי לספק טיפול טוב יותר מאי פעם.
דרישות הפריון והיעילות הדיגיטלית
ההסכם שנחתם במסגרת סקירת ההוצאות לשנת 2025 עבור שירות הבריאות הלאומי (NHS) מחייב שיפור שנתי בפריון בשיעור של 2% בשלוש השנים הקרובות. זהו שיפור הפריון המינימלי הנדרש כדי לספק את רמות הפעילות הנדרשות ולהשיג את יעדי הביצוע של הממשלה.
הטרנספורמציה הדיגיטלית היא מרכיב מרכזי בהשגת יעדים אלה. תוכנית הפריון של ה-NHS שואפת לצמצם את פער הפריון בטווח הקצר לרמות של שנת 2019/20, באמצעות שיפור הפריון התפעולי והקליני במוסדות בעלי הביצועים הנמוכים ביותר.
בטווח הארוך, התוכנית שואפת להביא לשיפור בפריון מעבר ל‘גבול הפריון’ הנוכחי — תוך קביעת סטנדרטים חדשים ליעילות בתחום הבריאות באמצעות אימוץ טכנולוגיות וייעול תהליכים.
| יעד הפריון | מסגרת זמן | מובילי דיגיטל |
|---|---|---|
| שיפור שנתי של 2% | 2025-2028 | מערכות EPR, אוטומציה, כלי בינה מלאכותית |
| לצמצם את הפער ביחס לקו הבסיס של שנת 2019/20 | טווח קצר (1–2 שנים) | יעילות תפעולית, תהליכי עבודה דיגיטליים |
| לשבור את גבולות הפריון | לטווח ארוך (3 שנים ומעלה) | ניתוח נתונים מתקדם, טיפול מונע |
עיבוד נתונים של שירותי בריאות קהילתיים
שירותי הבריאות הקהילתיים (CHS) הם מרכיב מרכזי במשימתו של שירות הבריאות הלאומי (NHS) לספק למטופלים טיפול איכותי, בטוח ומתואם קרוב יותר לביתם. עם זאת, מערכת הבריאות והטיפול אינה מצליחה להפיק באופן עקבי תובנות אמינות מנתוני ה-CHS ברמה הארצית, המערכתית או המקומית.
תוכנית הנתונים של שירותי הבריאות הקהילתיים של ה-NHS, המתוארכת ל-8 באפריל 2024 ועודכנה לאחרונה ב-27 במאי 2025, מטפלת בפער קריטי זה. מטרתה היא לייעל ולשפר את השירותים, את הטיפול בחולים ואת התוצאות בכל מסגרות הטיפול באמצעות הקמת מסגרות איתנות לאיסוף וניתוח נתונים.
לכך יש חשיבות מכיוון ששירותי הקהילה הם המקום שבו מתבצע בפועל המעבר מבית החולים לקהילה. ללא תשתית נתונים נאותה, תיאום הטיפול בין המסגרות השונות הופך לניחושים במקום לקבלת החלטות מבוססת ראיות.
הערכת בשלות דיגיטלית ויישום
הערכת הבשלות הדיגיטלית מספקת גישה מובנית להערכת מוכנותו של ארגון לתהליך של טרנספורמציה דיגיטלית. ה-NHS באנגליה פרסם הנחיות בנושא בשלות דיגיטלית ב-28 ביולי 2023, אשר עודכנו עד ל-30 באפריל 2025.
ההערכה מקיפה ממדים רבים, בהם גורמים טכנולוגיים, נוחות השימוש במערכת, ביצועים, יכולת התאמה, גמישות, אמינות, זמינות נתונים, שלמות נתונים וסודיות. כמו כן, היא בוחנת את דיוק הנתונים ואת מידת היעילות שבה ארגונים מנצלים כלים דיגיטליים לתמיכה בקבלת החלטות קליניות.
במסגרת מרפאות הכלליות, הבשלות הדיגיטלית נכללת ב"הנחיות לפרקטיקה נאותה" בנוגע לתיקים הרפואיים האלקטרוניים של רופאי המשפחה. הדבר מבטיח כי שירותי הרפואה הראשונית — השער הראשי לשירותי הבריאות הלאומיים (NHS) — יקפידו על סטנדרטים דיגיטליים אחידים בכל רחבי המערכת.
להפוך את מערכות ה-NHS לקלות יותר לעבודה
הטרנספורמציה הדיגיטלית בשירות הבריאות הלאומי (NHS) נתקלת לעתים קרובות בקשיים מעשיים – מערכות ישנות שאינן מתממשקות היטב, נתונים הפזורים על פני פלטפורמות שונות, ותהליכים שעדיין מסתמכים על פעולות ידניות. פערים אלה אינם משפיעים רק על היעילות, אלא גם על אופן שיתוף הפעולה בין הצוותים ועל מהירות קבלת ההחלטות. A-listware עובדת עם ארגונים כדי לבחון את אופן הפעולה של המערכות הקיימות, לזהות היכן נוצרים קשיים, ולהתאים את התהליכים כך שהמידע יזרום בצורה אמינה יותר בין הצוותים.
עבודתם מתמקדת בשיפור האופן שבו המערכות מתקשרות זו עם זו, ולא בהחלפת הכל בבת אחת. הדבר כולל ארגון מחדש של תהליכי העבודה, תמיכה באינטגרציה בין מערכות, ומודרניזציה הדרגתית של תשתית מיושנת מבלי לשבש את הפעילות השוטפת. אם יוזמות השינוי נראות איטיות או מקוטעות, כדאי לבחון מקרוב את המתרחש מאחורי הקלעים ולדון עם רשימת מוצרים א' איך להתקדם בצורה ברורה יותר.
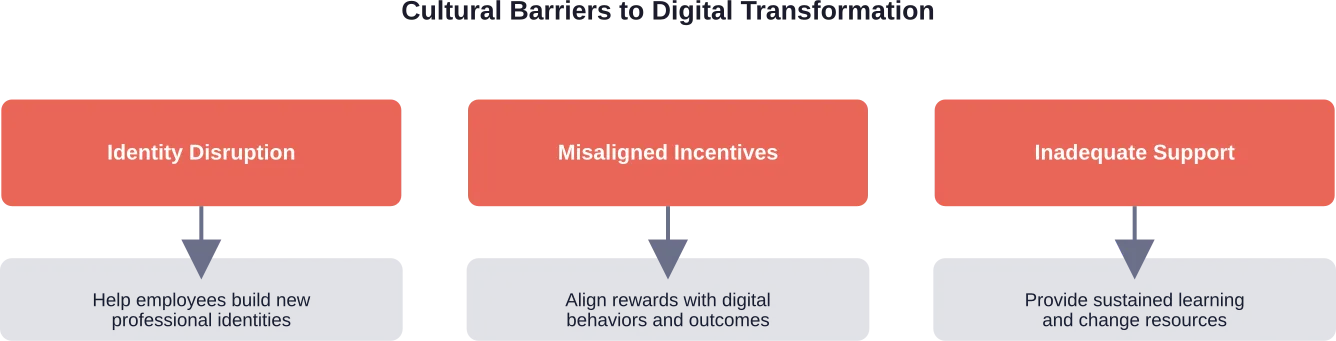
אתגרים ומכשולים ביישום
הטרנספורמציה הדיגיטלית בשירות הבריאות הלאומי (NHS) ניצבת בפני אתגרים משמעותיים החורגים מעבר לתחום הטכנולוגיה. משרד הביקורת הלאומי ציין שתוכניות מרכזיות קודמות הסתיימו בטרם עת מבלי שהשיגו את יעדיהן — תזכורת מאלפת לכך שכוונות טובות אינן מבטיחות הצלחה. והנה הסיבות לכך:
- מערכות ישנות מהוות מכשול משמעותי: חלק מתשתית ה-IT של ה-NHS מיושנת ולא יעילה, מה שהופך את האינטגרציה עם פלטפורמות מודרניות למשימה קשה ויקרה. עלות ההחלפה מתחרות עם סדרי העדיפויות הקליניים המיידיים.
- רמת המוכנות של כוח העבודה משתנה במידה רבה: הטרנספורמציה הדיגיטלית מחייבת את העובדים בכל הדרגים לאמץ דרכי עבודה חדשות, אך לעתים קרובות משאבי ההכשרה, התמיכה וניהול השינוי אינם מספיקים. התנגדות לשינוי היא תופעה טבעית, במיוחד בסביבות קליניות שבהן הלחץ רב.
- איכות הנתונים ותאימות בין מערכות נותרו בעיות מתמשכות: גם כאשר קיימות מערכות, תקני הנתונים משתנים, מה שמקשה על שיתוף מידע בצורה חלקה מעבר לגבולות הארגוניים. פלטפורמת הנתונים המאוחדת של ה-NHS שואפת לפתור בעיה זו באמצעות יצירת תשתית נתונים אחידה, אך יישומה מורכב.
- האמון הציבורי וההכללה מציגים מימד נוסף: שירותים דיגיטליים חייבים להיות נגישים לכלל האוכלוסייה, לרבות לאלה שחסרים להם כישורים דיגיטליים או גישה לאינטרנט. הדרת קבוצות פגיעות תפגע בעיקרון היסודי של שירותי בריאות אוניברסליים.
תמונת המצב בתחום ההשקעות והמימון
הממשלה התחייבה להשקעה חסרת תקדים בדיגיטליזציה של שירותי הבריאות הלאומיים (NHS). בנוסף ל-150 מיליון ליש"ט שהוקצו לדיגיטליזציה של שירותי הרווחה למבוגרים, תוכנית המימון הלאומית בהיקף של 4.7 מיליארד ליש"ט תומכת בשירותים דיגיטליים ובשיפור רמת הבשלות הדיגיטלית בכל רחבי המערכת.
ההשקעה הזו אינה מחולקת באופן שווה. קרנות מסוימות זוכות למימון ייעודי במסגרת תוכניות לאומיות, בעוד שאחרות נאלצות להתחרות על משאבים או לממן יוזמות דיגיטליות מכספן. מצב זה יוצר פערים ביכולות הדיגיטליות ברחבי אנגליה.
סקירת ההוצאות לשנת 2025 קושרת את המימון לשיפורים בפריון, ובכך יוצרת אחריות ישירה לתוצאות הטרנספורמציה הדיגיטלית. על הארגונים להוכיח שההשקעות בטכנולוגיה מתורגמות לעלייה מדידה ביעילות ולתוצאות טובות יותר עבור המטופלים.
תפקידם של בינה מלאכותית וטכנולוגיות מתקדמות
הבינה המלאכותית הופכת למרכיב מרכזי בשאיפות הטרנספורמציה הדיגיטלית של שירות הבריאות הלאומי (NHS). כלי בינה מלאכותית מסוגלים לנתח נתונים קליניים בהיקף נרחב, לזהות דפוסים שעלולים לחמוק מעיני בני אדם, ולתמוך בקבלת החלטות קליניות באמצעות המלצות מבוססות ראיות.
עם זאת, הטמעת בינה מלאכותית בתחום הבריאות מציבה אתגרים ייחודיים. בטיחות קלינית, הטיות אלגוריתמיות, פרטיות נתונים ואחריות על החלטות הנתמכות בבינה מלאכותית – כל אלה מצריכים מסגרות פיקוח קפדניות. על שירות הבריאות הלאומי (NHS) למצוא איזון בין חדשנות לבין בטיחות המטופלים ושיקולים אתיים.
תוכנית הבריאות לעשר השנים מדגישה את הצורך לנצל את ההזדמנויות שמציעות טכנולוגיות חדשות, תרופות וחידושים כדי לספק טיפול טוב יותר לכל המטופלים — בכל מקום בו הם גרים ובכל רמת הכנסה — וכן תמורה טובה יותר לכספי משלם המסים. הבינה המלאכותית היא חלק מובהק מחזון זה.
שאלות נפוצות
- מהו תהליך הטרנספורמציה הדיגיטלית בשירות הבריאות הלאומי (NHS)?
הטרנספורמציה הדיגיטלית בשירות הבריאות הלאומי (NHS) היא מעבר מקיף ממערכות בריאות אנלוגיות ומבוססות נייר לפלטפורמות דיגיטליות משולבות, המקשרות בין מטופלים, אנשי צוות רפואי ומסגרות טיפול. היא כוללת רשומות רפואיות אלקטרוניות, הזמנת תורים דיגיטלית, אפליקציית ה-NHS, ניתוח נתונים וכלים מבוססי בינה מלאכותית שנועדו לשפר את תוצאות הטיפול במטופלים ואת היעילות התפעולית.
- כמה אנשים משתמשים באפליקציית ה-NHS?
כיום, למעלה מ-28 מיליון אנשים הורידו את אפליקציית ה-NHS, ולמעלה מ-40 מיליון אנשים מחזיקים בחשבון ב-NHS. נתונים אלה מעידים על אימוץ נרחב של שירותי בריאות דיגיטליים ברחבי אנגליה, מה שהופך את האפליקציה לאחת הפלטפורמות הדיגיטליות הממשלתיות הנפוצות ביותר.
- מהן רשומות רפואיות אלקטרוניות (EPR)?
תיקי מטופלים אלקטרוניים הם מערכות דיגיטליות מקיפות המשלבות את ההיסטוריה הרפואית המלאה של המטופל, לרבות תוצאות בדיקות, תרופות, תוכניות טיפול, אלרגיות והיסטוריית טיפולים. כיום, לרוב מוסדות ה-NHS יש מערכות EPR, אם כי איכות היישום והבגרות הדיגיטלית משתנות מארגון לארגון.
- אילו יעדי תפוקה על שירות הבריאות הלאומי (NHS) לעמוד בהם?
ההסכם שנחתם במסגרת סקירת ההוצאות לשנת 2025 מחייב את שירות הבריאות הלאומי (NHS) להשיג שיפור שנתי בפריון בשיעור של 2% במשך שלוש שנים. זהו השיפור המינימלי הנדרש כדי לספק את רמות הפעילות הנדרשות ולהשיג את יעדי הביצוע של הממשלה. הטרנספורמציה הדיגיטלית היא מרכיב מרכזי בהשגת יעדים אלה באמצעות אוטומציה, שימוש טוב יותר בנתונים וייעול תהליכי העבודה.
- אילו אתגרים עומדים בפני המהפכה הדיגיטלית של ה-NHS?
בין האתגרים המרכזיים נמנים מערכות IT מיושנות, רמת מוכנות דיגיטלית משתנה בקרב כוח העבודה, בעיות באיכות הנתונים ובתאימות בין מערכות, חששות בנוגע לאמון הציבור ולשילוב דיגיטלי, וכן מימון לא אחיד בין הקרנות השונות. תוכניות דיגיטליות מרכזיות קודמות הסתיימו בטרם עת מבלי שהשיגו את יעדיהן, דבר המדגיש את המורכבות הכרוכה ביישום טכנולוגיות בריאות בקנה מידה נרחב.
- כיצד ממומן תהליך הטרנספורמציה הדיגיטלית?
ה-NHS מקבל מימון ממשלתי בסך 4.7 מיליארד ליש"ט עבור שירותים דיגיטליים ושיפורי תפקוד, כולל 150 מיליון ליש"ט המיועדים ספציפית לדיגיטליזציה של שירותי הרווחה למבוגרים. המימון מותנה בשיפורי פרודוקטיביות במסגרת "סקירת ההוצאות לשנת 2025", מה שמטיל אחריות על השגת תוצאות מדידות מההשקעות בטכנולוגיה.
- מהי הערכת בשלות דיגיטלית?
הערכת הבשלות הדיגיטלית בוחנת את מוכנותו של ארגון להגיב לשינויים טכנולוגיים ולשלב מערכות חדשות. ההנחיות של שירות הבריאות הלאומי באנגליה (NHS England) מתייחסות לשימושיות המערכת, לביצועיה, לזמינות הנתונים, לאבטחה, ולמידת היעילות שבה ארגונים משתמשים בכלים דיגיטליים לצורך קבלת החלטות קליניות. הערכות אלו מסייעות בזיהוי פערים ובקביעת סדר עדיפויות לתחומי שיפור.
סיכום: הדרך קדימה
הטרנספורמציה הדיגיטלית עבור שירות הבריאות הלאומי (NHS) מהווה הן הזדמנות אדירה והן אתגר משמעותי. התשתית הולכת ומתגבשת — 28 מיליון משתמשים באפליקציית ה-NHS, רשומות רפואיות אלקטרוניות ברוב המוסדות, ומיליארדי ליש"ט שהוקצו למימון. הכיוון האסטרטגי ברור, כפי שבא לידי ביטוי בשלושת השינויים המרכזיים של "תוכנית הבריאות לעשר שנים".
אך הטכנולוגיה לבדה לא תביא לשינוי. ההצלחה תלויה בהכנת כוח העבודה, בהבטחת איכות הנתונים ותאימותם, בשמירה על אמון הציבור, ובלמידה מכישלונות העבר. יעד הפריון 2% יוצר תחושת דחיפות, אך שינוי בר-קיימא דורש סבלנות והתמדה.
עבור אנשי מקצוע בתחום הבריאות, מנהלים וקובעי מדיניות, השאלה אינה האם תתרחש מהפכה דיגיטלית – היא כבר בעיצומה. השאלה היא האם היא תיושם באופן מחושב, מכליל ויעיל מספיק כדי לממש את ההבטחה לטיפול טוב יותר לכל המטופלים ולתמורה טובה יותר עבור משלמי המסים.
אמנם ההישגים עד כה מעורבים, אך ההימור מעולם לא היה גבוה יותר. שירות הבריאות הלאומי (NHS) שיצליח לעבור את המהפכה הדיגיטלית בהצלחה יוכל לקבוע סטנדרטים עולמיים למתן שירותי בריאות במאה ה-21.