Quick Summary: Digital transformation for sales is the strategic integration of digital technologies into every aspect of sales operations to improve efficiency, customer experience, and revenue growth. It encompasses automating repetitive tasks, leveraging data analytics for insights, adopting AI-powered tools, and reimagining traditional sales processes for the modern buyer. Successful digital sales transformation balances technology adoption with human relationships while measuring ROI through comprehensive KPIs beyond just productivity.
The way companies sell has fundamentally changed. What worked five years ago doesn’t cut it anymore.
Buyers now expect personalized experiences, instant responses, and seamless digital interactions throughout their journey. Sales teams that cling to outdated methods find themselves outpaced by competitors who’ve embraced digital transformation. But here’s the thing—digital transformation in sales isn’t just about adopting the latest tools. It’s about reimagining the entire sales operation for the digital age.
According to Statista data from 2020, 37% of companies were expected to grow the digitization of the customer experience. That was six years ago. Today, digitization isn’t optional—it’s the baseline.
What Is Digital Transformation for Sales?
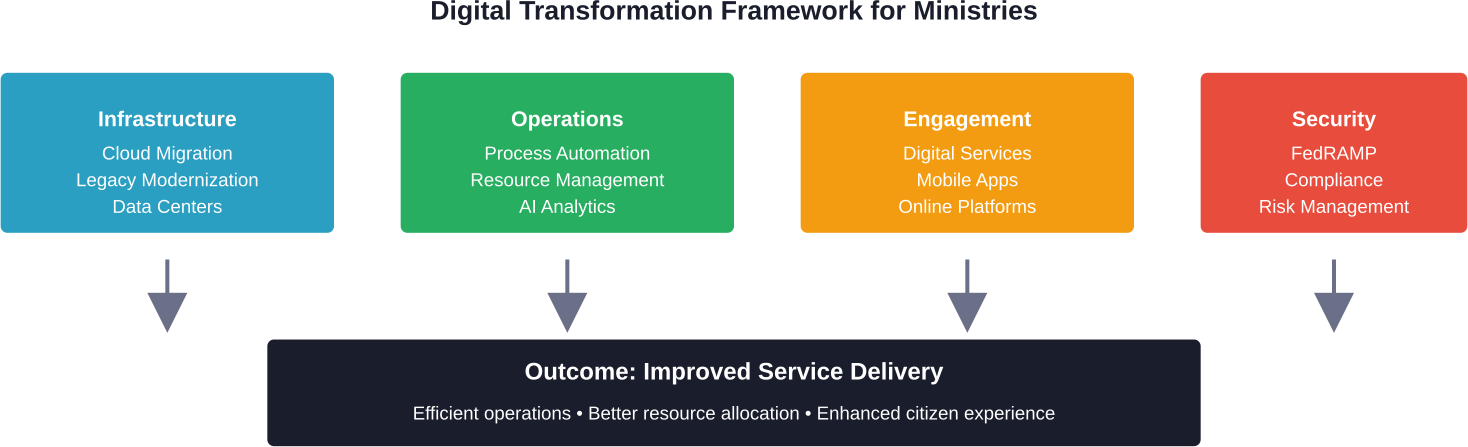
Digital sales transformation is the process of integrating digital technologies into all aspects of a company’s sales operations. Think of it as a subset of broader digital transformation initiatives, but focused specifically on how organizations sell, engage prospects, and grow revenue.
This goes beyond just buying a CRM or setting up email automation. Real transformation touches everything: prospecting methods, customer engagement strategies, sales collateral delivery, proposal generation, pricing negotiations, and post-sale relationship management.
The goal? Making sales processes more efficient while simultaneously improving the customer experience. Sales teams that get this right don’t just work faster—they work smarter, closing deals that matter while building stronger relationships.
The Core Components
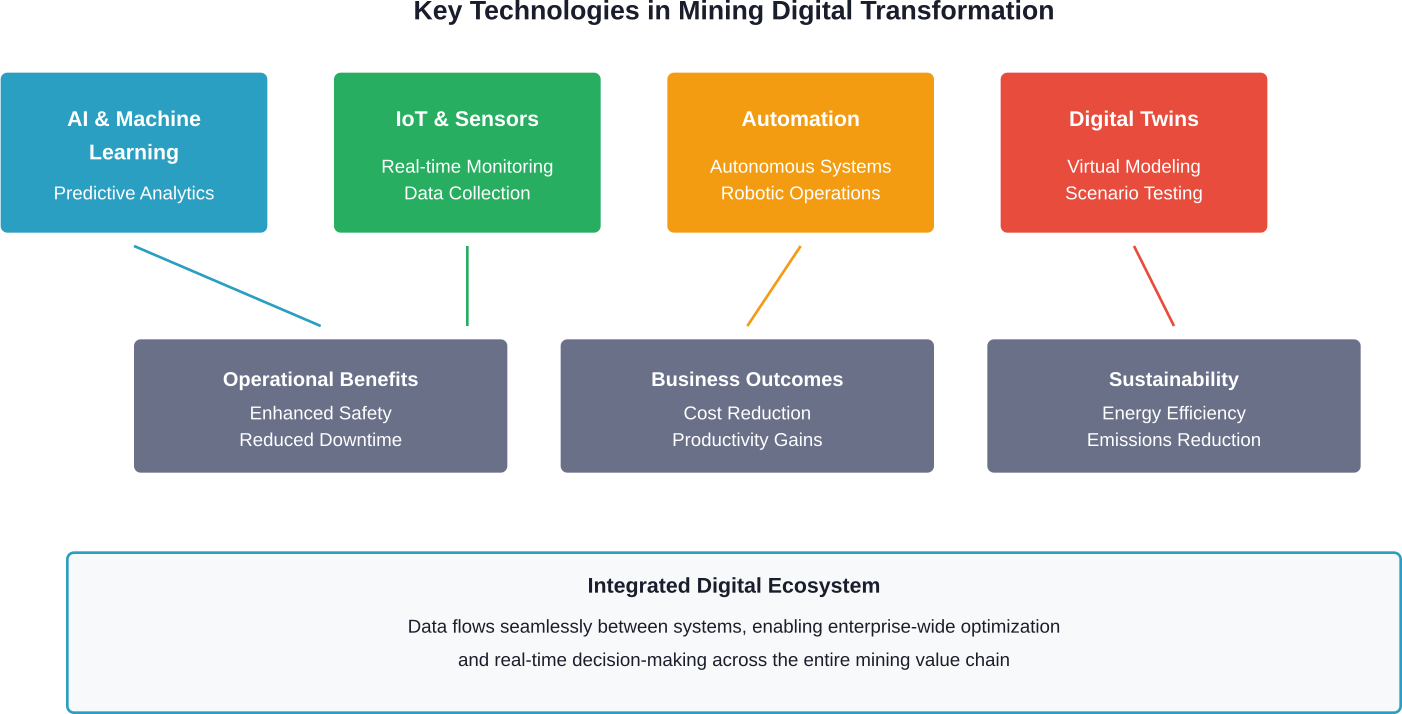
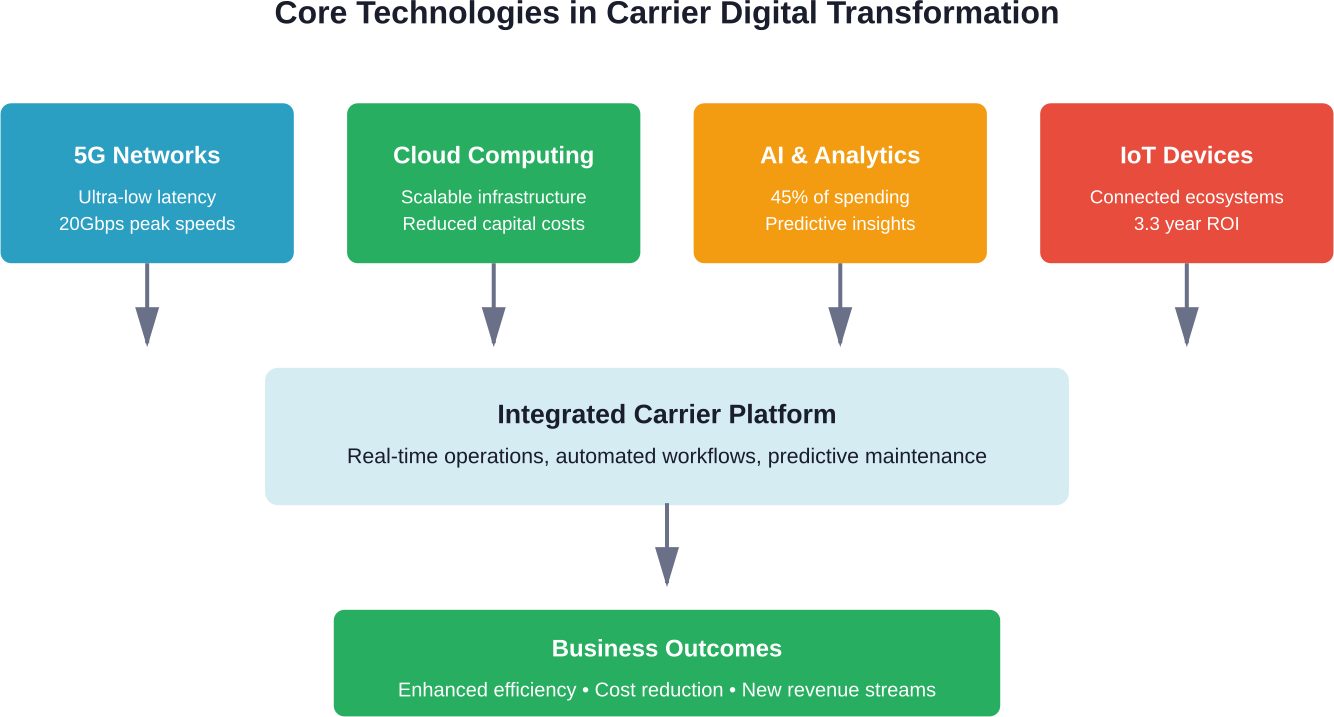
Digital transformation in sales typically involves several key elements working together:
- Automation of repetitive tasks that waste sellers’ time on non-selling activities
- Data analytics and insights that reveal customer behavior patterns and sales opportunities
- AI-powered tools for forecasting, lead scoring, and personalization at scale
- Digital-first customer engagement across multiple channels and touchpoints
- Integrated technology stacks that eliminate silos between sales, marketing, and customer success
Research from UAB Collat School of Business highlights how AI is reshaping sales strategies across various stakeholder groups. Sales teams leveraging these technologies report higher efficiency and responsiveness compared to those relying on traditional methods alone.
Why Digital Transformation Matters for Sales Teams
Customer expectations have shifted dramatically. According to Salesforce research, over half of customers said technology has significantly changed their expectations of how companies should interact with them. More specifically, 73% prefer doing business with brands that personalize their experience.
That’s a tall order for sales teams using spreadsheets and generic email templates.
Digital transformation addresses this gap. It enables sales organizations to meet modern buyers where they are—online, mobile, researching independently—while providing the personalized attention those buyers demand.
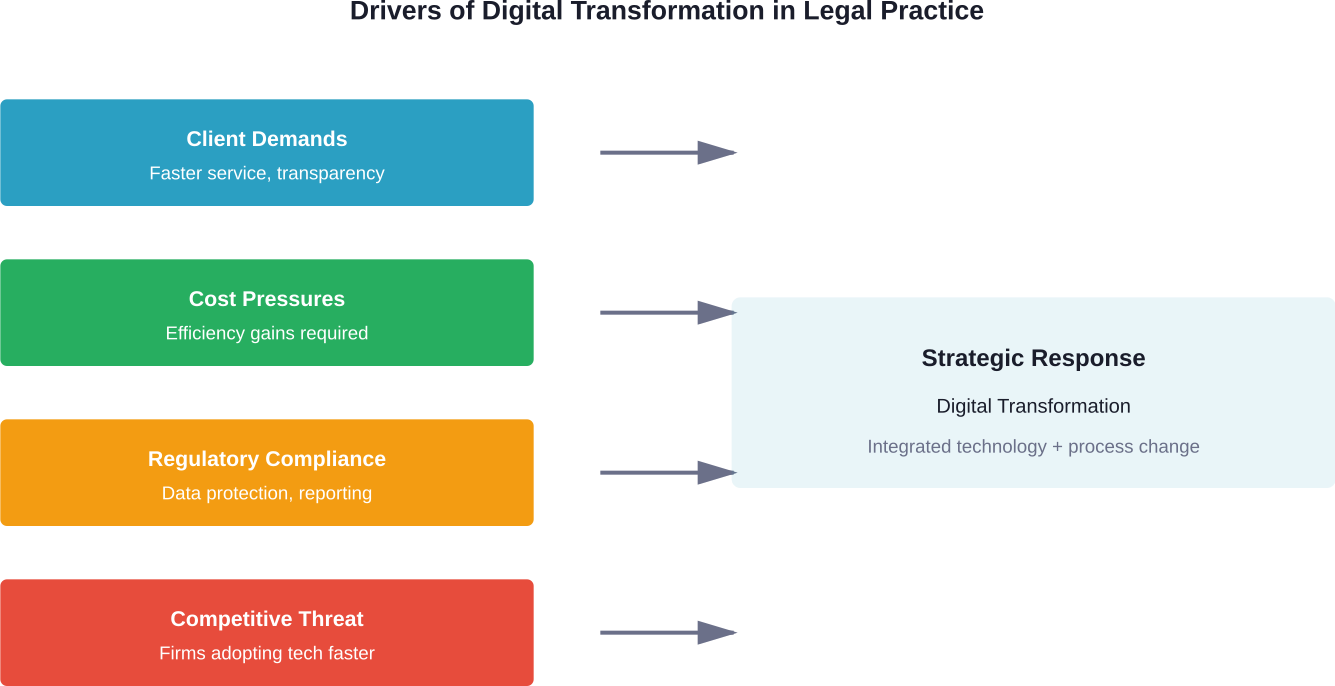
The Competitive Imperative
MIT CISR research on digital transformation identified what they call “future-ready” firms—organizations that have transformed on both customer experience and operational efficiency dimensions. These top performers report average revenue growth of 17.3 percentage points and a net margin of 14.0 percentage points above their industry average.
Those aren’t small differences. They’re the kind of advantages that determine market leaders versus followers.
Companies that delay digital transformation in sales don’t just miss opportunities for growth. They actively cede ground to competitors who can respond faster, personalize better, and close more efficiently.
The Role of AI in Sales Transformation
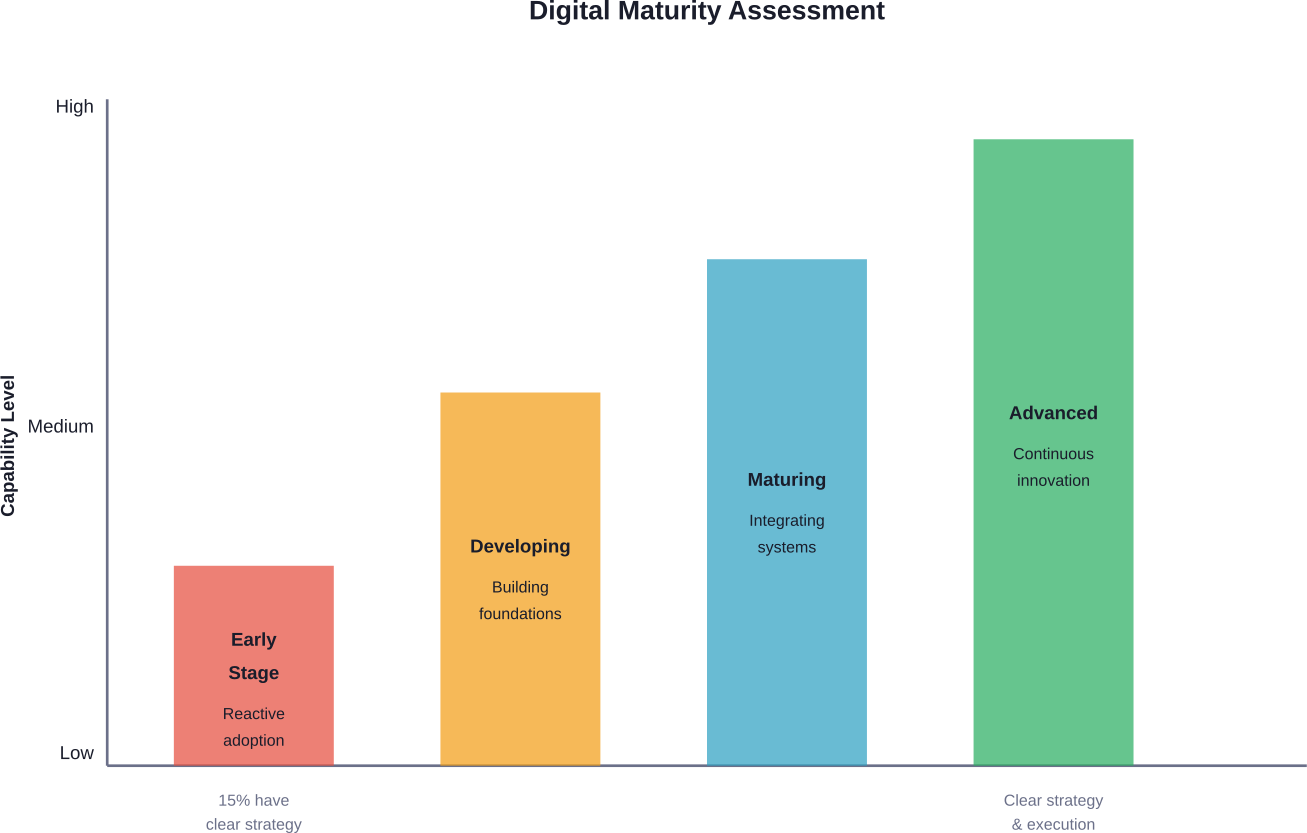
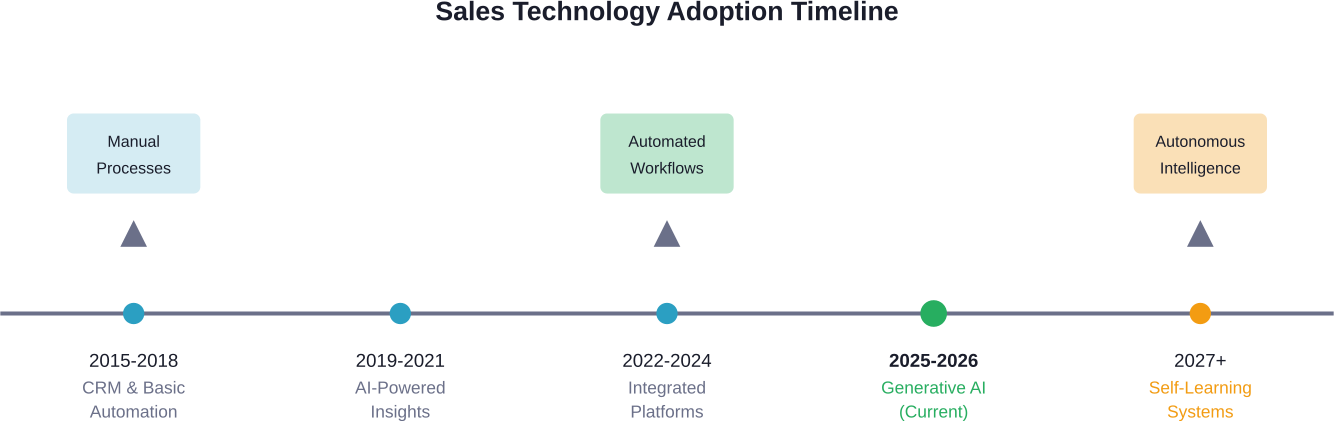
Artificial intelligence has become a central pillar of digital sales transformation. But adoption remains uneven and understanding remains limited.
According to research from California Management Review, only some of sales leaders feel confident in their understanding of generative AI, according to California Management Review research. Adoption rates correlate strongly with company size—large enterprises are 48 times more likely to deploy Sales AI than smaller firms, according to California Management Review research.
How Sales AI Creates Value
Sales AI reshapes the sales landscape by revolutionizing how organizations identify opportunities, engage prospects, and optimize performance. The technology excels in several specific applications:
- Lead scoring and prioritization: AI algorithms analyze historical data to predict which prospects are most likely to convert, allowing sales teams to focus their energy where it matters most.
- Personalization at scale: Machine learning enables customized outreach to thousands of prospects simultaneously—something impossible through manual effort alone.
- Forecasting accuracy: AI-powered forecasting models incorporate far more variables than traditional methods, improving prediction reliability for pipeline and revenue.
- Conversation intelligence: Natural language processing analyzes sales calls to identify successful techniques, coaching opportunities, and compliance risks.
Real talk: AI won’t replace human salespeople. The Berkeley research emphasizes balancing AI effectiveness with human-led relationships. Technology handles data-heavy analytical tasks while humans focus on relationship building, complex negotiation, and strategic thinking.
The Adoption Challenge
Despite AI’s potential, implementation faces real obstacles. Many sales organizations struggle with data quality issues, integration complexity, and change management resistance.
Gartner predicts that by 2028, 60% of B2B sales seller work will be executed by AI (GenAI). This suggests companies often implement new technologies without fundamentally transforming underlying processes—a common pitfall.
Successful AI adoption in sales requires more than just deploying tools. It demands process redesign, ongoing training, and cultural shifts toward data-driven decision making.
Key Strategies for Digital Sales Transformation
Transformation doesn’t happen by accident. It requires deliberate strategy and systematic execution across multiple dimensions.
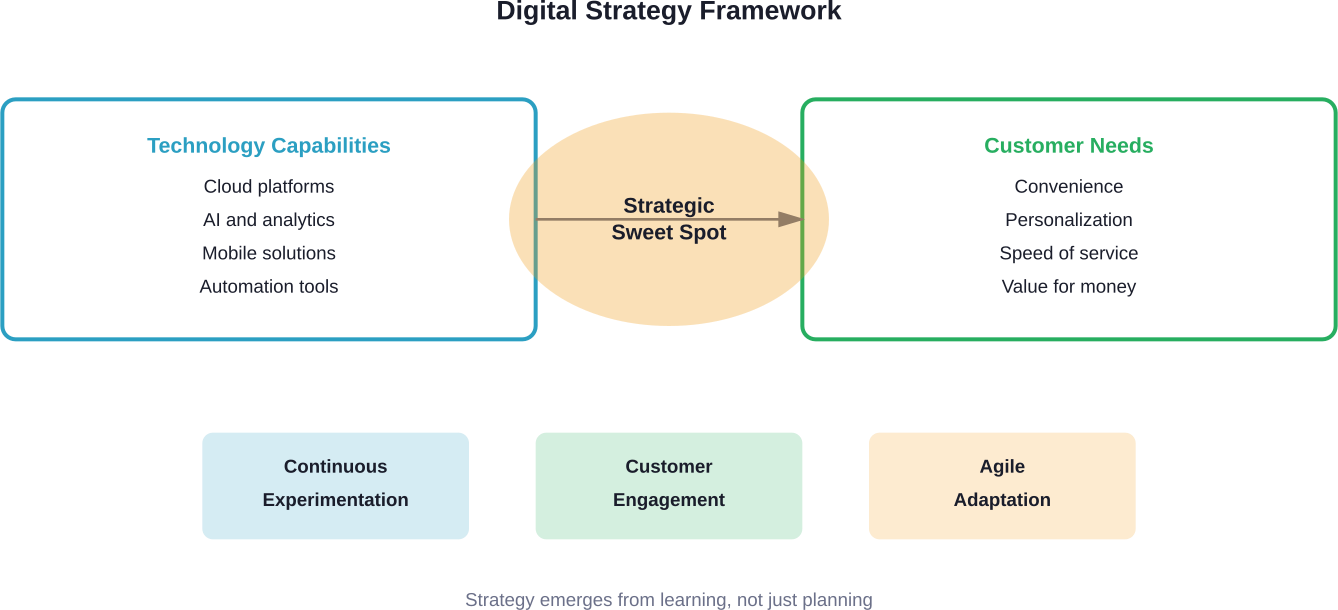
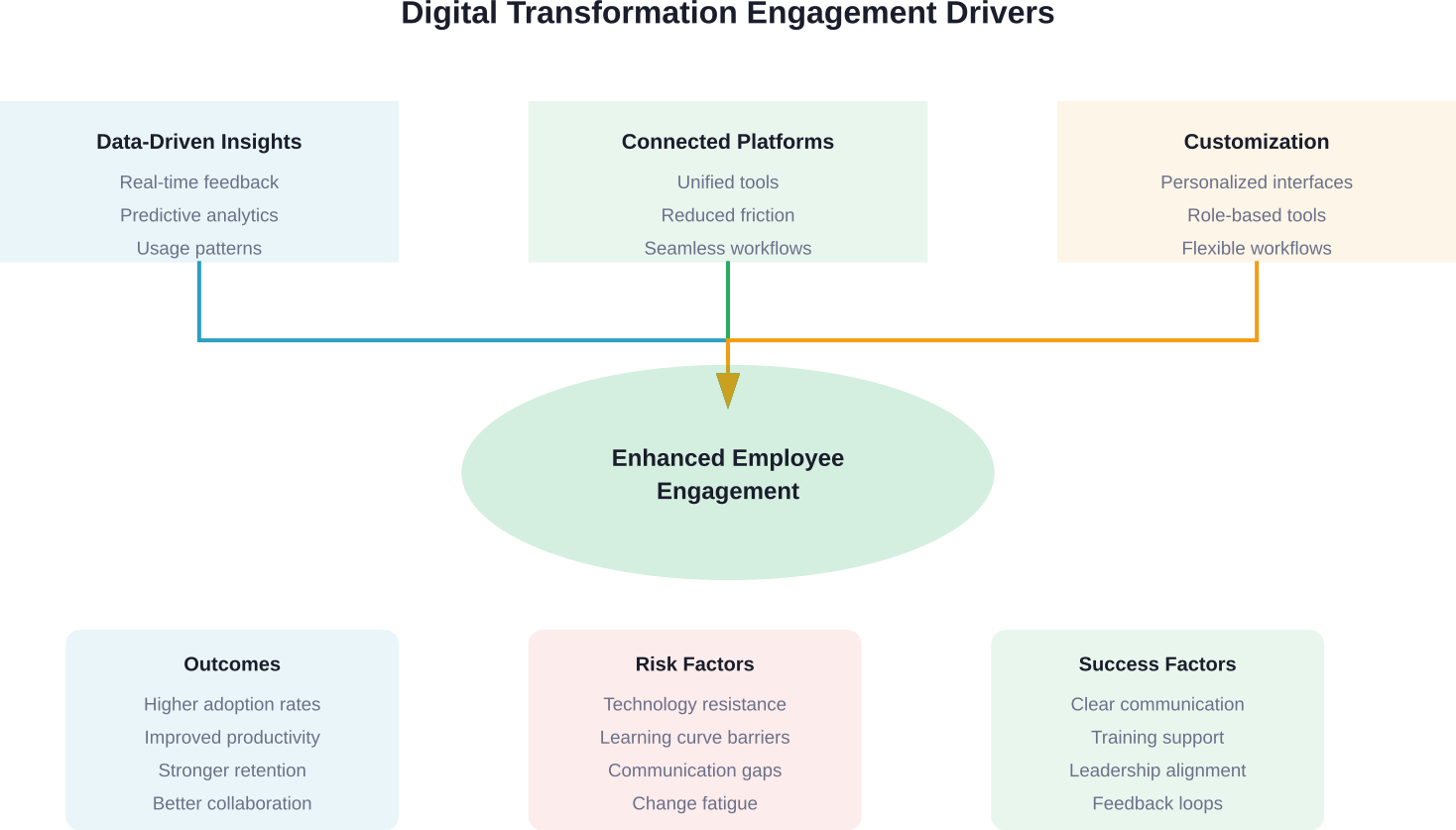
Start With Customer Experience
The best digital transformations begin with understanding what customers actually want. Modern buyers expect seamless omnichannel experiences, instant access to information, and personalized interactions that respect their time.
Sales teams should map the entire customer journey—from initial awareness through purchase and beyond—identifying friction points where digital tools could improve the experience. Where do prospects drop off? When do they request information that could be self-served? What manual processes create delays?
This customer-centric approach ensures technology investments actually solve real problems rather than just adding complexity.
Automate Low-Value Activities
Sales professionals spend too much time on administrative tasks instead of selling. Data entry, meeting scheduling, proposal generation, follow-up reminders—these necessary but low-value activities eat up hours every week.
Digital transformation should aggressively automate these repetitive tasks. CRM systems that auto-capture email interactions, AI assistants that schedule meetings, proposal software that generates quotes from templates—these tools free up time for actual customer engagement.
The goal isn’t just efficiency. It’s refocusing human talent on high-value activities where people excel: building relationships, solving complex problems, and strategic thinking.
Leverage Data for Insights
Sales teams generate enormous amounts of data—customer interactions, deal progression, win/loss patterns, engagement metrics. Most of this valuable information goes underutilized.
Effective digital transformation harnesses this data for actionable insights. Which marketing channels produce the best leads? What deal characteristics predict successful closes? Which customer segments offer the highest lifetime value? How do top performers differ from average ones?
Analytics platforms can answer these questions, but only if organizations invest in data quality, integration, and analysis capabilities. Garbage data produces garbage insights.
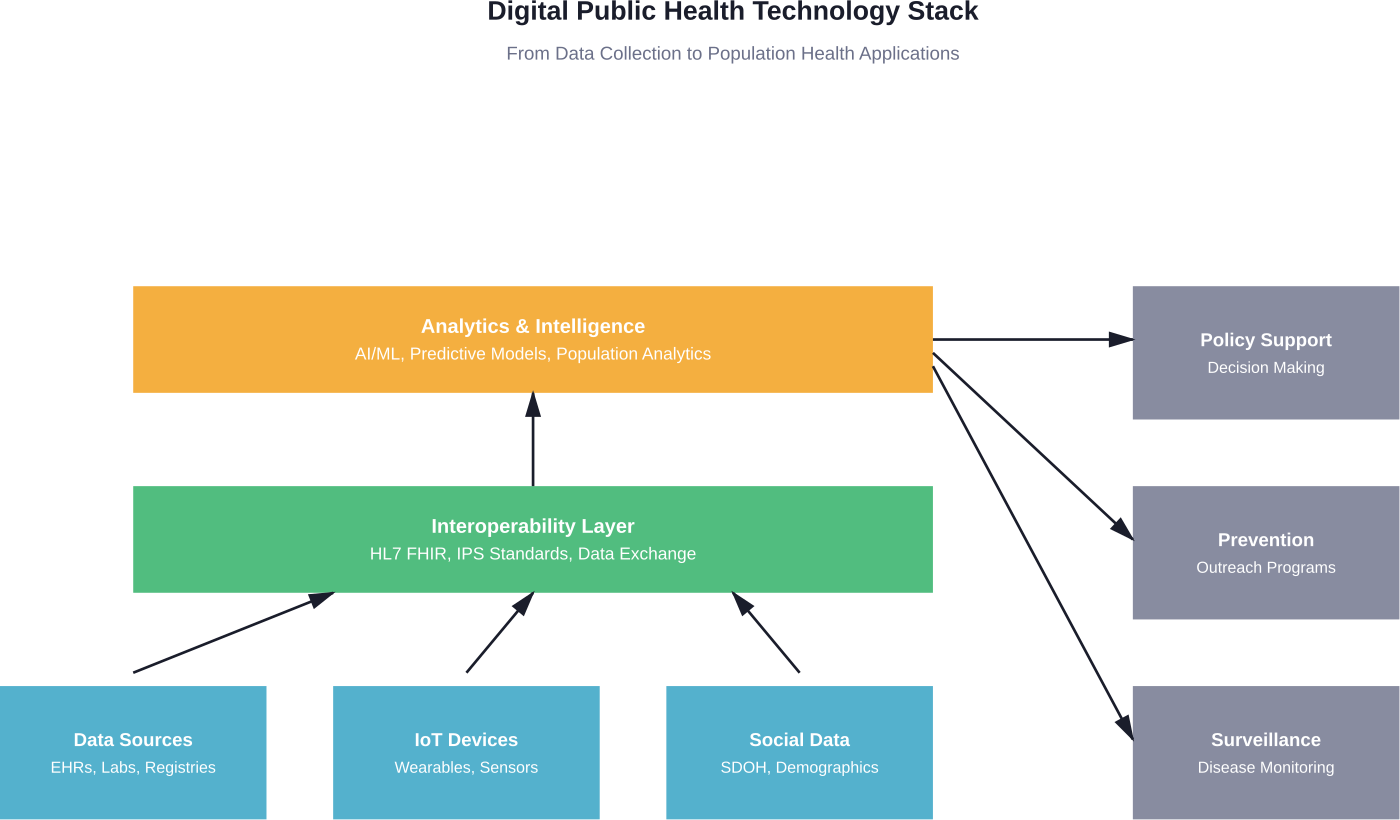
Build Integrated Technology Stacks
Sales doesn’t operate in isolation. Modern selling requires tight coordination between sales, marketing, customer success, and operations.
Digital transformation should break down silos through integrated technology stacks where data flows seamlessly between systems. Marketing automation platforms connect to CRMs, which integrate with customer success tools, which feed back into product development.
This integration creates a unified view of each customer, eliminates duplicate data entry, and ensures everyone works from the same information. According to Forrester research on revenue enablement, only 45% of REP owners effectively surface ‘what to show’ and ‘what to know’ assets for sellers at each buyer journey inflection point, indicating widespread taxonomy and asset management challenges.
Develop Digital-First Capabilities
MIT CISR research identified ten capabilities that future-ready firms develop to accelerate digital transformation. While the full list spans both customer and operational dimensions, several prove particularly relevant for sales:
| Capability | Sales Application | Impact |
|---|---|---|
| Operational Excellence | Streamlined sales processes with minimal friction | Faster deal cycles, higher productivity |
| Data-Driven Decision Making | Analytics-based territory planning and forecasting | Better resource allocation, accuracy |
| Rapid Experimentation | A/B testing outreach strategies and messaging | Continuous improvement, optimization |
| Customer Obsession | Personalized engagement based on behavior data | Higher conversion rates, loyalty |
| Technology Integration | Unified sales tech stack eliminating silos | Complete customer view, efficiency |
Developing these capabilities requires sustained investment in people, processes, and technology—not just one-time tool purchases.
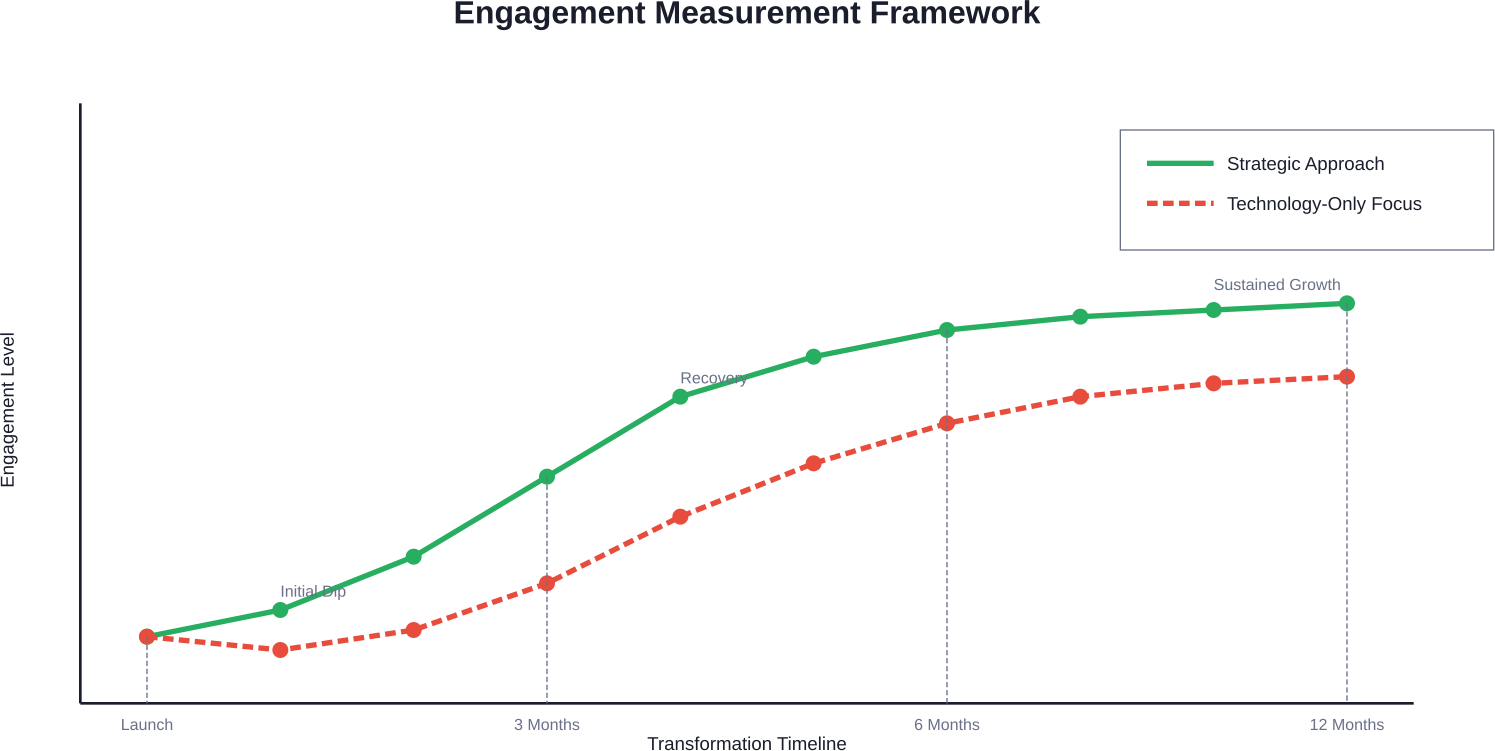
Measuring Digital Transformation ROI
How do organizations know if their digital transformation actually works? Measurement matters.
According to Deloitte research, 81% of organizations use productivity as the primary measure of digital transformation ROI. But that’s far too narrow. Organizations with a more holistic mindset are 20% more likely to attribute medium-to-high enterprise value to their digital transformations.
Deloitte identified a taxonomy of 46 digital transformation KPIs. The most comprehensive measurement frameworks track metrics across multiple dimensions:
Financial Metrics
- Revenue growth and deal size increases
- Sales cycle length reduction
- Customer acquisition cost decreases
- Profit margin improvements
- Customer lifetime value growth
Operational Metrics
- Sales productivity and time allocation
- Process cycle times and automation rates
- Technology adoption and utilization rates
- Data quality and completeness scores
- System integration and uptime metrics
Customer Metrics
- Customer satisfaction and NPS scores
- Retention and churn rates
- Engagement levels across channels
- Response time and issue resolution speed
- Personalization effectiveness measures
In healthcare specifically, Deloitte research shows how targeted personalization through digital transformation can drive significant financial benefits. A health plan with 500,000 members could potentially increase annual revenue by $55 million to $150 million through reduced churn rates of customer service inbound calls.
That’s the kind of impact that makes transformation investments pay off.
The Attribution Challenge
Here’s where it gets tricky. Digital transformation initiatives often run alongside other business changes, making direct attribution difficult. Did revenue increase because of the new CRM, the improved compensation plan, or favorable market conditions?
Sophisticated organizations address this through controlled experiments where possible, baseline comparisons, and multivariate analysis. They also track leading indicators—adoption rates, user satisfaction, process compliance—that predict eventual business outcomes.
The key is establishing clear baseline metrics before transformation begins and tracking consistently throughout implementation.
Common Challenges and How to Overcome Them
Digital transformation sounds great in theory. In practice, most initiatives face significant obstacles.
Legacy System Constraints
Many organizations wrestle with outdated systems that don’t integrate well with modern tools. These legacy platforms create data silos, slow processes, and limit what’s possible.
The solution rarely involves ripping everything out and starting fresh. That’s too risky and expensive. Instead, successful transformations use middleware and APIs to connect old and new systems, gradually modernizing the stack over time.
Change Resistance
Sales professionals often resist new tools and processes, particularly when they’ve found success with existing methods. This resistance can kill even well-designed transformations.
Overcoming resistance requires involving sales teams early in the planning process, clearly communicating benefits, providing adequate training, and demonstrating quick wins. Transformation works best when it’s done with salespeople, not to them.
Data Quality Issues
AI and analytics only work well with clean, accurate data. Many organizations discover their data quality falls short when they begin transformation initiatives.
Addressing this requires both technology solutions—deduplication tools, validation rules, enrichment services—and process changes like mandatory field completion and regular data hygiene reviews.
Skills Gaps
Digital transformation often requires capabilities the current team lacks. Data analysis, technology administration, process design—these skills may not exist in traditional sales organizations.
Organizations can address gaps through hiring, training existing staff, or partnering with external specialists. The important thing is recognizing the gap and addressing it rather than assuming people will figure it out.
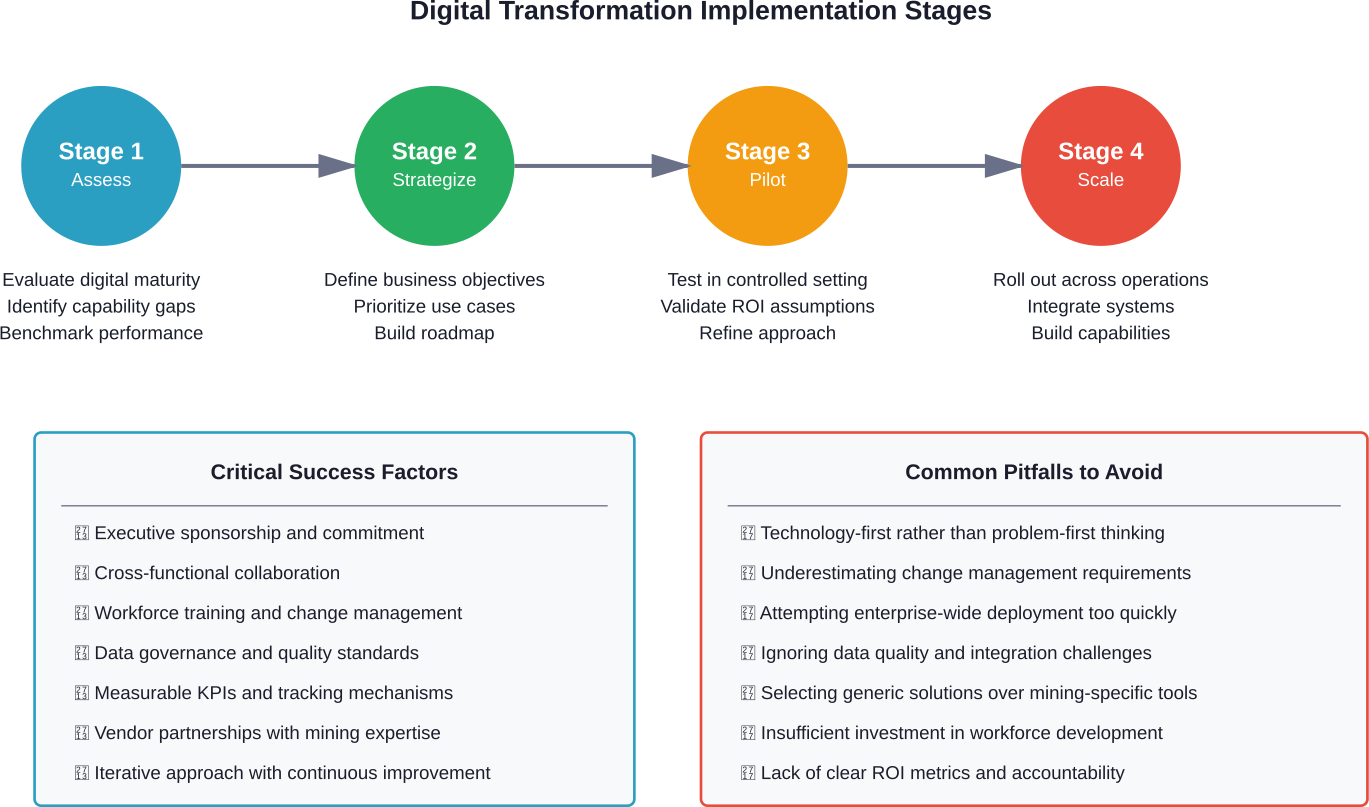
Unclear Strategy
Some organizations jump into digital transformation by buying tools without clear strategy. They end up with expensive technology that doesn’t drive results.
Successful transformation starts with strategy: What specific business outcomes are we targeting? Which processes need to change? How will we measure success? Technology selection comes after these questions are answered.
| Challenge | Impact | Solution Approach |
|---|---|---|
| Legacy Systems | Data silos, slow processes | API integration, phased modernization |
| Change Resistance | Low adoption, wasted investment | Early involvement, clear communication, training |
| Data Quality | Inaccurate insights, poor AI performance | Validation rules, deduplication, enrichment |
| Skills Gaps | Underutilized capabilities, slow progress | Targeted hiring, upskilling, external partners |
| Unclear Strategy | Misaligned tools, unclear ROI | Define objectives first, then select technology |
The Human Element in Digital Sales
Here’s what too many organizations forget: digital transformation isn’t about replacing people with technology. It’s about augmenting human capabilities.
The Berkeley research on Sales AI emphasizes balancing AI effectiveness with human-led relationships. Technology excels at data processing, pattern recognition, and task automation. Humans excel at empathy, complex problem solving, and relationship building.
The best digital sales operations leverage both.
What Humans Do Best
Even in highly digital sales environments, certain activities remain fundamentally human:
- Building trust and rapport: Authentic relationship building requires emotional intelligence, empathy, and personal connection—things AI can’t replicate.
- Navigating complex negotiations: High-stakes deals with multiple stakeholders and competing interests demand human judgment and flexibility.
- Creative problem solving: When customers have unique requirements or challenges, human creativity and experience find solutions technology might miss.
- Strategic account management: Long-term customer relationships built on deep understanding and mutual value creation remain human endeavors.
What Technology Does Best
Technology should handle the tasks that don’t require human judgment but consume significant time:
Data entry and CRM updates. Lead research and qualification. Meeting scheduling and follow-up reminders. Proposal generation from templates. Performance tracking and reporting. Pattern recognition across large datasets.
When technology handles these activities, sales professionals can focus their energy where they create the most value—with customers.
Future Trends in Digital Sales Transformation
Digital transformation isn’t a one-time project. Technology continues evolving, creating new capabilities and opportunities.
Generative AI Expansion
Generative AI tools are becoming more sophisticated and sales-specific. Beyond generic chatbots, we’re seeing AI that drafts personalized emails, creates custom proposals, generates meeting summaries, and even coaches sellers in real-time during calls.
But remember—only 21% of sales leaders currently feel confident in their understanding of generative AI. As the technology matures and education improves, adoption will accelerate.
Self-Learning Systems
According to Forrester research, the industry is moving toward self-discovering AI taxonomy for revenue enablement tools. These systems would automatically learn which content assets correlate with successful deals, continuously optimizing recommendations without manual configuration.
When this capability becomes mainstream, it’ll be a game-changer for sales enablement effectiveness.
Deeper Integration
Technology stacks will continue consolidating and integrating. Rather than managing ten separate tools with manual data transfers, sales teams will work with unified platforms where data flows automatically between functions.
This integration creates the single source of truth organizations need for accurate forecasting, complete customer views, and efficient operations.
Privacy and Trust Focus
As digital selling becomes more data-driven, privacy and trust concerns grow more important. Regulations like GDPR set baselines, but customers increasingly expect transparency about how their data is used.
Future digital sales transformation will need to balance personalization capabilities with clear privacy protections and ethical data practices.
Building a Transformation Roadmap
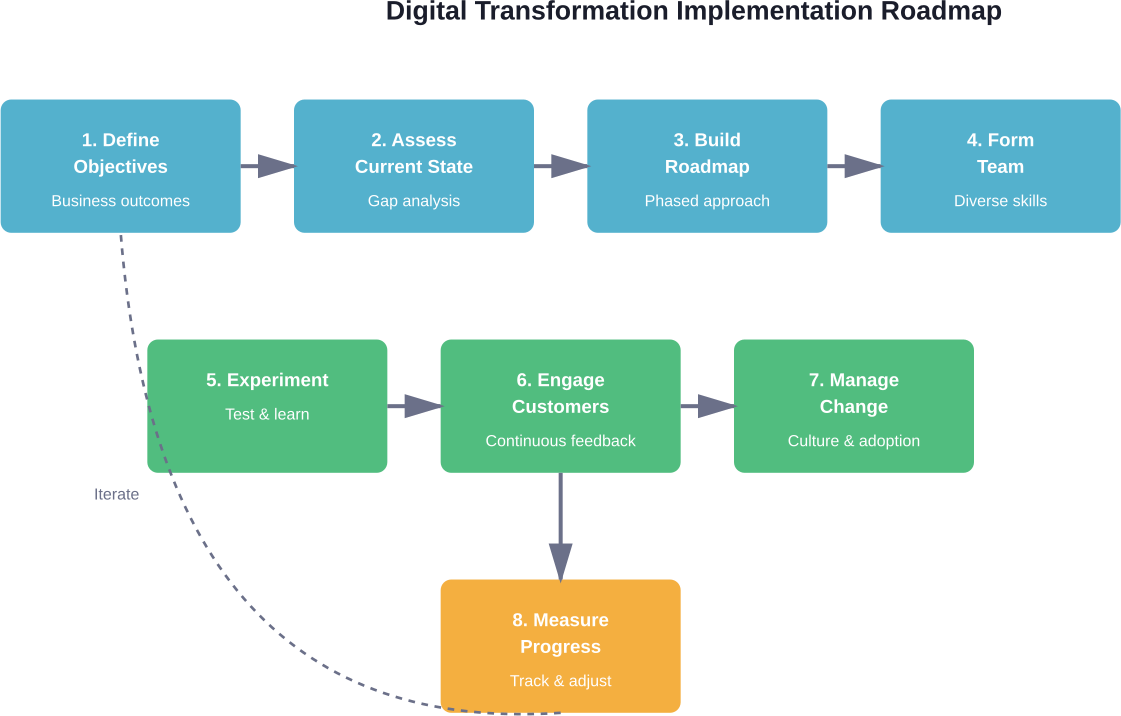
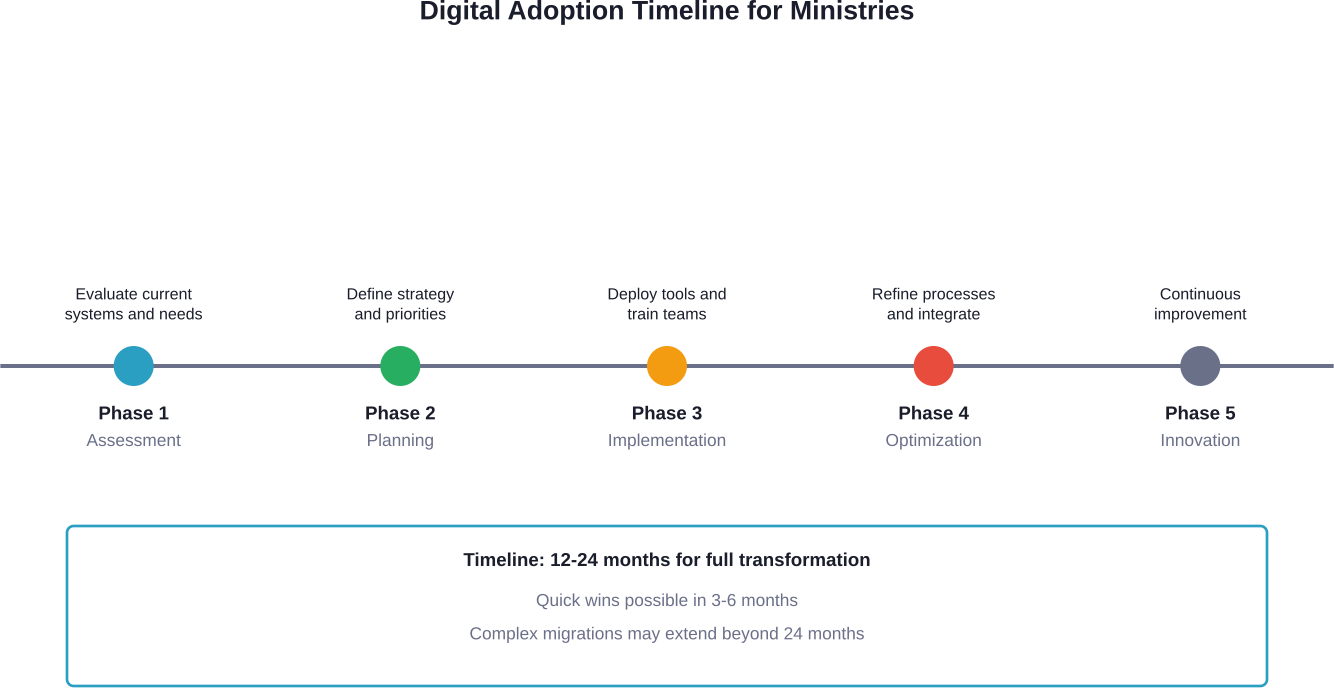
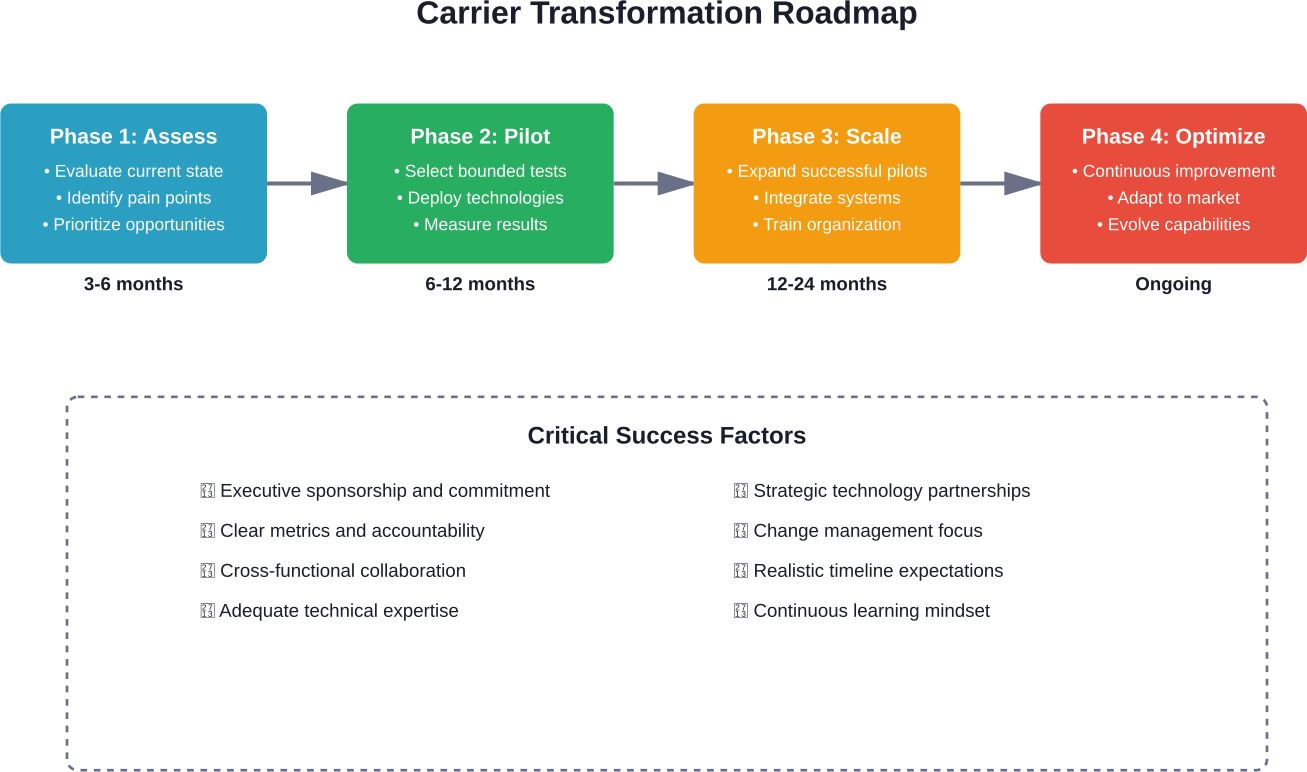
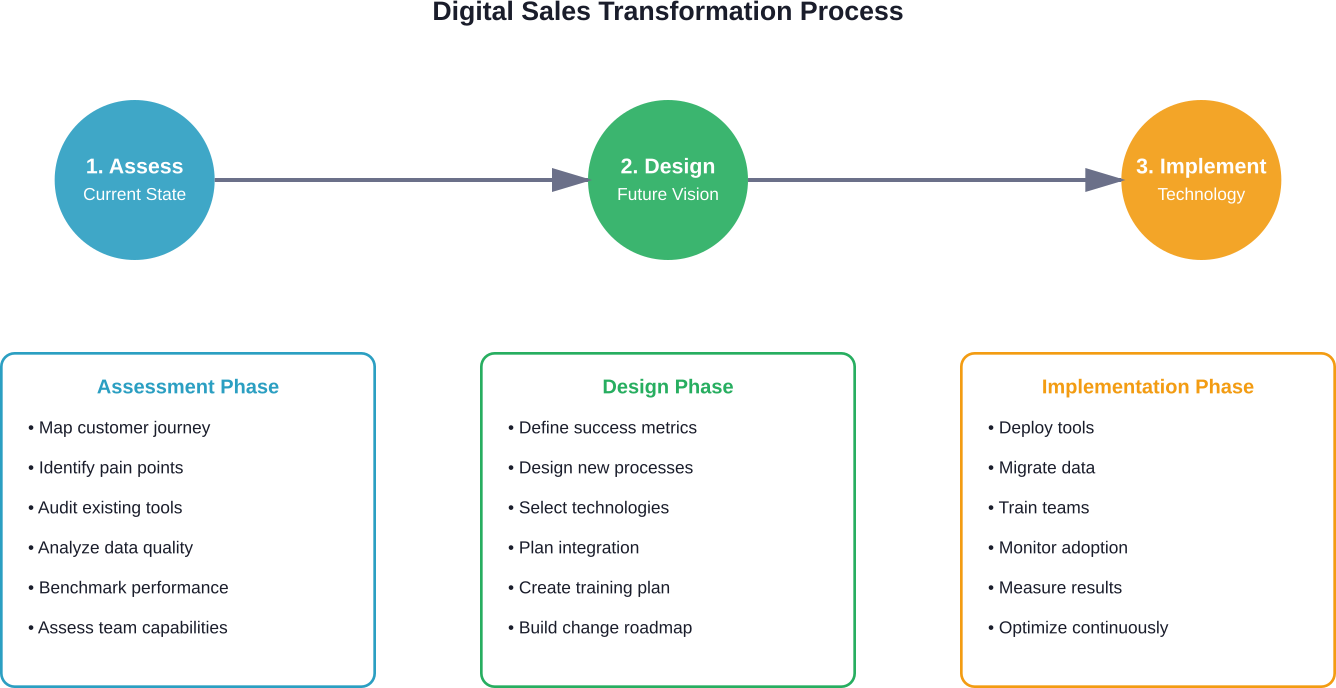
So where should organizations start? Effective digital transformation follows a deliberate roadmap rather than random tool adoption.
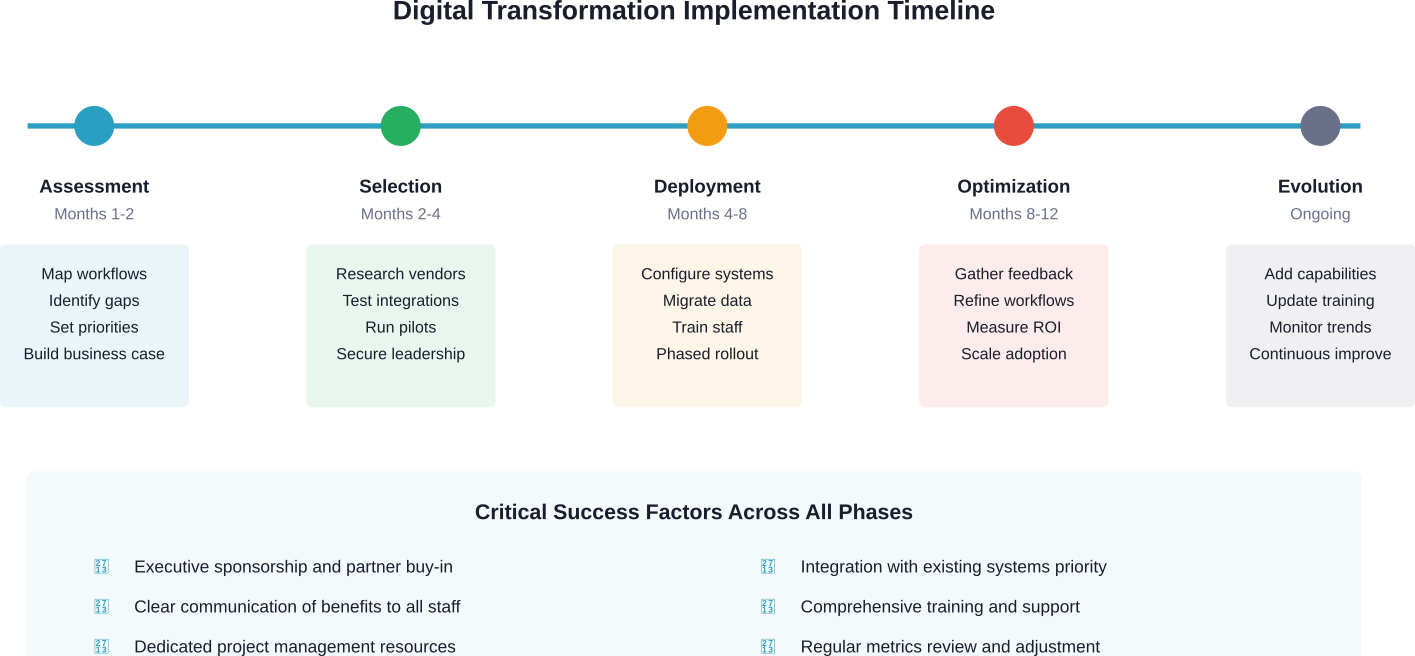
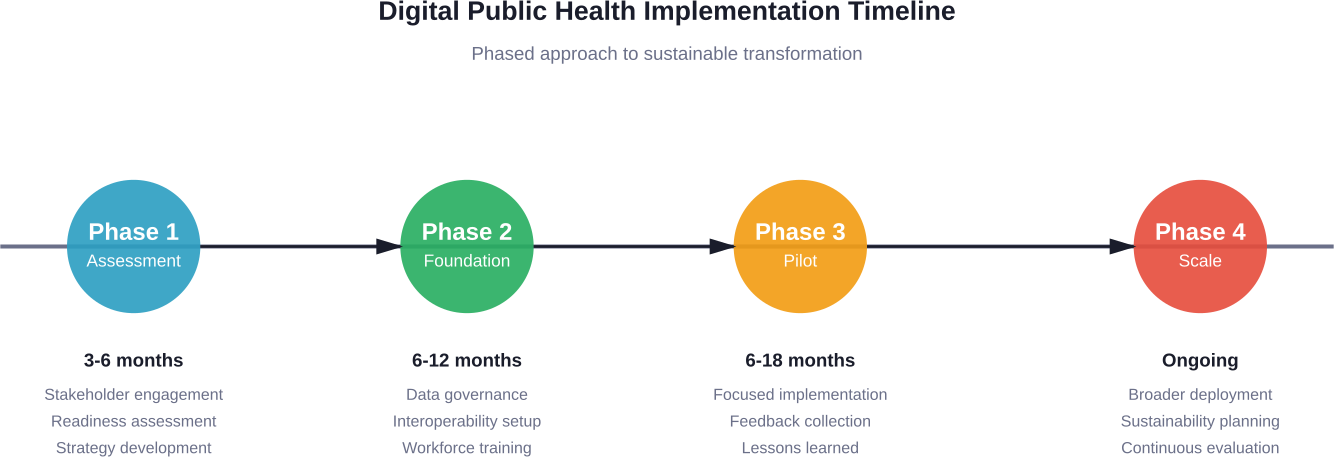
Phase 1: Foundation (Months 1-3)
Assess current state across processes, technology, data, and capabilities. Map the customer journey identifying pain points. Audit existing tools for gaps and overlaps. Establish baseline metrics. Define clear objectives and success criteria.
This foundation phase prevents the common mistake of buying solutions before understanding problems.
Phase 2: Quick Wins (Months 3-6)
Identify high-impact, low-complexity improvements that deliver fast results. These might include automating specific manual tasks, implementing email templates, or improving data quality in key fields.
Quick wins build momentum and demonstrate value, making it easier to secure support for longer-term initiatives.
Phase 3: Core Transformation (Months 6-18)
Deploy major technology platforms, redesign core processes, integrate systems, migrate data, and train teams extensively. This phase requires significant investment and change management.
Break this phase into manageable increments rather than attempting everything simultaneously. Phased rollouts reduce risk and allow learning along the way.
Phase 4: Optimization (Month 18+)
Monitor performance against established KPIs, gather user feedback, identify optimization opportunities, and continuously refine processes and configurations.
Digital transformation never really ends. Technology evolves, business needs change, and new opportunities emerge. The optimization phase becomes an ongoing operating model.
Start Your Sales Digital Transformation with A-listware
Sales teams often struggle with fragmented tools, outdated CRM setups, and manual reporting. Digital transformation usually starts by fixing that foundation. A-listware works with companies that want to modernize internal systems, connect sales data across departments, and build software that supports faster, more transparent sales operations. Their team typically begins by reviewing current workflows and infrastructure, then designing a practical transformation plan that may include CRM integration, automation, analytics, and custom platform development.
The same approach applies to customer-facing sales environments such as e-commerce or retail platforms. A-listware helps businesses integrate modern technologies, improve how customer data is used, and build systems that give sales teams clearer insight into performance. If your sales infrastructure still depends on disconnected tools or legacy systems, A-listware can help restructure the technical side of the sales process so it actually supports growth.
If you want to modernize how your sales organization works, contact A-listware to help you turn scattered tools and manual processes into a connected digital sales system.
Frequently Asked Questions
- What is digital transformation for sales?
Digital transformation for sales is the strategic integration of digital technologies into all aspects of sales operations to improve efficiency, customer experience, and revenue growth. It involves automating repetitive tasks, leveraging data analytics for insights, adopting AI-powered tools, and reimagining traditional sales processes for modern buyers. The goal is making sales teams more effective while simultaneously enhancing customer interactions.
- How long does sales digital transformation take?
Most comprehensive sales digital transformation initiatives take 12-24 months for core implementation, though optimization continues indefinitely. The timeline depends on organization size, existing technology maturity, scope of changes, and resource availability. Quick wins can often be achieved within 3-6 months to build momentum, while full transformation across processes, technology, and culture requires longer investment.
- What’s the ROI of digital sales transformation?
According to MIT CISR research, future-ready firms that successfully transform report average revenue growth of 17.3 percentage points and a net margin of 14.0 percentage points above industry averages. However, ROI varies significantly based on implementation quality, industry context, and measurement approach. Organizations that use holistic KPIs beyond just productivity are 20% more likely to attribute medium-to-high enterprise value to their transformations, according to Deloitte research.
- Do we need to replace our entire sales team for digital transformation?
No. Digital transformation augments human capabilities rather than replacing people. The U.S. Census Bureau’s 2023 Annual Business Survey (referring to 2022 data) indicated that only 3.8% of businesses used AI, and while impact on employment was limited due to low adoption, firms using AI often reported a need for higher skill levels. The focus should be on training existing teams to work effectively with new tools while leveraging technology to handle data-heavy tasks, freeing salespeople to focus on relationship building and strategic activities where humans excel.
- What are the biggest challenges in digital sales transformation?
Common challenges include legacy system constraints that create data silos, change resistance from sales teams comfortable with existing methods, poor data quality that undermines AI and analytics, skills gaps in areas like data analysis and technology administration, and unclear strategy that leads to misaligned tool purchases. Successful transformations address these through phased modernization, early stakeholder involvement, data quality initiatives, targeted training, and clear strategic planning before technology selection.
- How important is AI in sales transformation?
AI has become central to digital sales transformation, though adoption remains uneven. Sales AI enables lead scoring and prioritization, personalization at scale, improved forecasting accuracy, and conversation intelligence for coaching. However, only a part of sales leaders feel confident in their understanding of generative AI according to California Management Review research. Success requires balancing AI effectiveness with human-led relationships—technology handles analytical tasks while humans focus on relationship building and complex problem solving.
- Should small businesses pursue digital sales transformation?
Yes, though the scope and approach may differ from enterprise initiatives. Small businesses face the same customer expectations for digital experiences and personalized interactions. However, resource constraints mean focusing on high-impact areas first: basic automation of repetitive tasks, CRM implementation for better data management, and customer-centric process improvements. Small businesses can often move faster than large enterprises due to less complexity, turning size into an advantage during transformation.
Conclusion: The Path Forward
Digital transformation for sales isn’t optional anymore. Customer expectations, competitive pressures, and technology capabilities have fundamentally changed the selling landscape.
Organizations that cling to traditional methods fall behind—gradually at first, then dramatically. The performance gap between future-ready firms and laggards continues widening as digital capabilities compound over time.
But successful transformation requires more than just buying the latest tools. It demands strategic thinking about what customers need, honest assessment of current capabilities, deliberate process redesign, and sustained investment in people development alongside technology deployment.
The good news? Organizations don’t need to transform everything overnight. Start with clear objectives, focus on high-impact areas, demonstrate quick wins, and build from there. Each improvement creates momentum for the next.
Digital sales transformation balances technology effectiveness with human strengths. AI handles data analysis, automation eliminates repetitive tasks, and analyzes surface insights—freeing sales professionals to focus on what they do best: building relationships, solving complex problems, and creating value for customers.
That combination of human expertise and digital capability defines the future of sales. The organizations that master this balance will dominate their markets. Those that don’t will wonder what happened.
Ready to transform your sales operations? Start by assessing where you are today, defining where you want to go, and identifying the first high-impact changes that will move you forward. The technology exists, the roadmap is proven, and the results speak for themselves.