Résumé rapide : La transformation numérique pour la sécurité intègre des mesures de cybersécurité tout au long des efforts de modernisation organisationnelle, en protégeant les données, les systèmes et les opérations à mesure que les entreprises adoptent l'infrastructure cloud, les technologies d'IA et les processus digital-first. Selon les cadres NIST et CISA, la transformation sécurisée nécessite des architectures de confiance zéro, une surveillance continue et des approches basées sur les risques qui traitent la sécurité comme un pilier fondamental plutôt que comme une réflexion après coup.
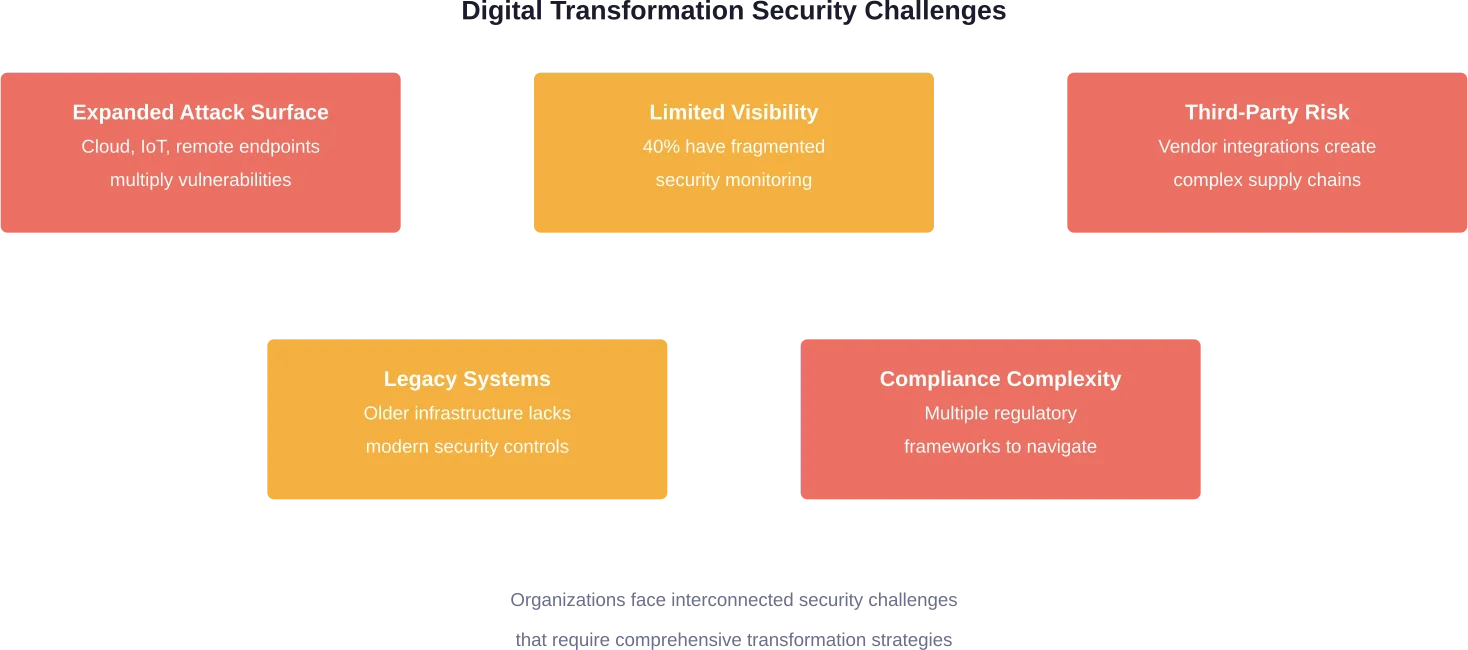
Les organisations du monde entier accélèrent leurs initiatives de transformation numérique. Mais voilà : alors que les entreprises se précipitent pour adopter les services cloud, l'intelligence artificielle et les technologies IoT, elles élargissent en même temps leurs surfaces d'attaque.
La question n'est plus de savoir s'il faut transformer numériquement. Il s'agit de savoir comment le faire en toute sécurité.
Selon le rapport SANS State of ICS/OT Security 2025, seulement 14 % des organisations se sentent pleinement préparées aux nouvelles menaces cybernétiques dans leurs environnements opérationnels. C'est une statistique inquiétante quand on sait que plus d'une organisation sur cinq (21,5%) a déclaré avoir subi un incident de cybersécurité au cours de l'année écoulée, et que quatre de ces événements sur dix ont entraîné des perturbations opérationnelles.
La sécurité ne peut pas être ajoutée après coup. Elle doit être intégrée au tissu de la transformation dès le premier jour.
Qu'est-ce que la transformation numérique pour la sécurité ?
La transformation numérique de la sécurité représente l'intégration stratégique des principes, des technologies et des pratiques de cybersécurité à chaque phase de la modernisation de l'organisation. Il ne s'agit pas d'ajouter des pare-feu à l'infrastructure en nuage, mais de repenser fondamentalement la façon dont la sécurité fonctionne dans les environnements numériques.
Les modèles de sécurité traditionnels supposent un périmètre de réseau défini. Les employés travaillaient au bureau, les applications étaient hébergées dans des centres de données et les équipes de sécurité pouvaient tracer des limites claires autour de ce qui devait être protégé.
Cette époque est révolue.
Les organisations modernes opèrent dans des environnements de cloud hybride, prennent en charge des effectifs à distance et intègrent constamment des services tiers. Selon le modèle de maturité de la confiance zéro de la CISA, l'objectif est d'empêcher l'accès non autorisé aux données et aux services en appliquant des décisions d'accès par demande précises et avec le moins de privilèges possible, même lorsque le réseau est considéré comme déjà compromis.
La transformation numérique sécurisée s'appuie sur des technologies telles que le cloud computing, la mobilité et l'apprentissage automatique pour favoriser l'agilité tout en sécurisant chaque point de connexion. Les organisations doivent moderniser simultanément leurs opérations commerciales et leur posture de sécurité.
Améliorer la sécurité grâce à la transformation numérique
La transformation de la sécurité ne fonctionne que lorsque les systèmes sont correctement construits et entretenus. A-listware fournit des équipes d'ingénieurs spécialisés pour aider à mettre en œuvre des architectures sécurisées et les soutenir à long terme.
Forte de son expérience dans les technologies d'entreprise et les plates-formes en nuage, l'équipe apporte son soutien :
- la modernisation des systèmes existants
- la mise en œuvre d'environnements sécurisés en nuage
- l'intégration de la surveillance et du contrôle d'accès
- la maintenance et la mise à l'échelle de l'infrastructure critique pour la sécurité
En fonction des besoins du projet, l'équipe peut s'intégrer dans les flux de travail existants ou prendre en charge des composants spécifiques du système. Contacter A-listware pour discuter de votre transformation en matière de sécurité et obtenir le soutien technique adéquat.
Pourquoi la cybersécurité est au cœur de la transformation numérique
Les données sont devenues extrêmement précieuses. Non seulement pour les entreprises et les clients, mais aussi pour les cybercriminels qui cherchent à en tirer profit. Une étude réalisée en 2020 par le Ponemon Institute a révélé que plus de 80 % des participants pensent que les données de leur entreprise ont pris de la valeur au fil du temps.
L'augmentation de la valeur s'accompagne d'une augmentation du risque.
La transformation numérique crée de nouvelles vulnérabilités. La migration vers le cloud expose les données à différents vecteurs de menace. Les appareils IoT multiplient les points de terminaison qui nécessitent une surveillance. Le travail à distance élimine le périmètre traditionnel du réseau. L'intelligence artificielle introduit de nouvelles surfaces d'attaque et amplifie les menaces existantes.
L'expansion rapide de l'IA, des technologies intelligentes et de l'infrastructure en nuage a fait entrer la transformation numérique mondiale dans une nouvelle phase. Ce qui était autrefois facultatif est devenu essentiel à la survie.
Selon les normes ISO sur la sécurité de l'information, les organisations doivent considérer la protection des données comme une pierre angulaire de la création de valeur à une époque définie par l'interconnexion numérique. Cette ressource inestimable est confrontée à des menaces constantes de la part de cybercriminels de plus en plus sophistiqués et d'envergure mondiale.
L'évolution du paysage des menaces
Les acteurs de la menace ne restent pas inactifs. Ils font évoluer leurs techniques parallèlement aux avancées technologiques légitimes.
L'analyse des techniques d'attaque émergentes réalisée par le SANS Institute lors du RSAC 2025 a mis en évidence des menaces qui mêlent sophistication technique, perturbation opérationnelle et incertitude juridique. Les défenseurs doivent se préparer à affronter des adversaires qui exploitent les mêmes technologies de transformation numérique que celles mises en œuvre par les organisations.
Seulement 13 % des personnes interrogées ont déclaré avoir une visibilité totale de la chaîne de destruction cybernétique des SCI, tandis que plus de 40 % ont décrit leur visibilité comme étant partielle et fragmentée, avec des lacunes importantes.
Sans visibilité globale, les renseignements sur les menaces ne peuvent être appliqués efficacement. Les organisations peuvent avoir une connaissance théorique des risques, mais ne disposent pas du contexte opérationnel nécessaire pour agir sur la base de cette connaissance.
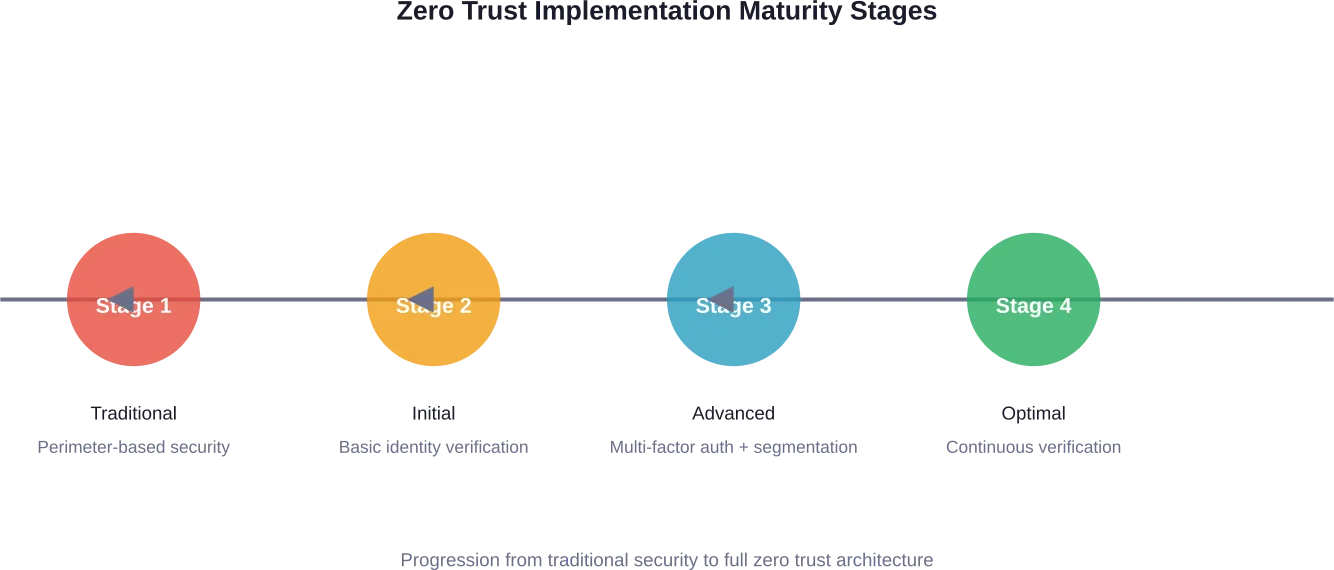
Mise en œuvre d'une architecture de confiance zéro
La confiance zéro s'est imposée comme le modèle de sécurité fondamental pour la transformation numérique. Le concept est simple : ne jamais faire confiance, toujours vérifier.
Le modèle de maturité de la confiance zéro de la CISA fournit un ensemble de concepts conçus pour minimiser l'incertitude dans l'application de décisions d'accès précises et avec le moins de privilèges possible. Cette approche part du principe que le réseau est déjà compromis et exige une vérification pour chaque demande d'accès, quelle qu'en soit l'origine.
Cela est important car les modèles de sécurité traditionnels basés sur le périmètre s'effondrent dans les environnements cloud et hybrides. Lorsque les applications se trouvent dans plusieurs nuages, que les données circulent entre différents services et que les employés travaillent de n'importe où, il n'y a pas de périmètre unique à défendre.
L'architecture de confiance zéro répond à ce problème en mettant en œuvre plusieurs principes clés :
- Vérifier explicitement en utilisant tous les points de données disponibles pour l'authentification
- Appliquer l'accès au moindre privilège pour limiter les autorisations des utilisateurs au strict nécessaire.
- Supposons une brèche et minimisons le rayon de l'explosion grâce à la segmentation.
- Inspecter et enregistrer tout le trafic pour une surveillance continue
- Utiliser le cryptage partout où les données sont déplacées ou conservées
Le cadre de cybersécurité du NIST complète la confiance zéro en aidant les organisations à mieux comprendre et à améliorer leur gestion des risques de cybersécurité grâce à une approche structurée de l'identification, de la protection, de la détection, de la réponse et de la récupération des menaces.
Intégrer la sécurité dans la transformation de l'informatique en nuage
L'adoption du cloud s'accélère. Les réseaux 5G offrant des vitesses allant jusqu'à 10 Gbps, les employés peuvent accéder aux applications et aux données plus rapidement sur les réseaux mobiles qu'à travers les connexions traditionnelles des bureaux.
Mais la transformation de l'informatique dématérialisée introduit des considérations uniques en matière de sécurité. Les modèles de responsabilité partagée signifient que les organisations doivent comprendre quels sont les contrôles de sécurité qui leur appartiennent et ceux qui sont gérés par les fournisseurs de services en nuage. Les erreurs de configuration restent l'une des causes les plus fréquentes d'incidents liés à la sécurité de l'informatique dématérialisée.
La transformation sécurisée de l'informatique en nuage nécessite :
- Systèmes de gestion des identités et des accès fonctionnant dans des environnements hybrides
- Des politiques de classification et de protection des données qui suivent l'information partout où elle se déplace
- Surveillance de la sécurité offrant une visibilité sur les charges de travail et les services en nuage
- Automatisation de la conformité pour maintenir les exigences réglementaires sur l'ensemble des plates-formes
- Plans de réponse aux incidents adaptés aux architectures cloud-natives
Les organisations doivent également tenir compte de la manière dont les différents modèles de services en nuage - IaaS, PaaS, SaaS - influent sur leurs responsabilités en matière de sécurité. Plus le fournisseur gère, moins les équipes de sécurité ont un contrôle direct sur l'infrastructure sous-jacente.
| Composant de sécurité | Infrastructure traditionnelle | Environnement en nuage |
|---|---|---|
| Sécurité physique | L'organisation gère | Le prestataire gère |
| Contrôles du réseau | Contrôle total | Responsabilité partagée |
| Gestion de l'identité | Répertoire sur place | IAM en nuage |
| Cryptage des données | L'organisation met en œuvre | L'organisation configure |
| Contrôle de conformité | Audits manuels | Outils de conformité automatisés |
| Réponse aux incidents | Accès direct aux systèmes | Enquête basée sur l'API |
Gérer la sécurité dans le cadre d'une transformation pilotée par l'IA
L'intelligence artificielle est en train de remodeler les opérations commerciales et la cybersécurité. Les organisations intègrent l'IA dans leurs produits, leurs services et leurs processus internes à un rythme sans précédent.
Cela crée un paradoxe. L'IA renforce les capacités de sécurité en améliorant la détection des menaces, la réponse automatisée et l'analyse comportementale. Simultanément, elle introduit de nouvelles vulnérabilités et amplifie les risques existants.
Les adversaires utilisent l'IA pour concevoir des campagnes de phishing plus convaincantes, automatiser la découverte de vulnérabilités et échapper aux contrôles de sécurité traditionnels. L'écart de sophistication se réduit à mesure que les outils d'IA se banalisent et deviennent accessibles aux acteurs de la menace disposant d'une expertise technique limitée.
Selon une analyse récente, la forte dépendance à l'égard de tiers dans le cadre de la transformation pilotée par l'IA aggrave ces risques. Les organisations intègrent souvent des services d'IA provenant de fournisseurs sans comprendre pleinement les implications de ces dépendances en matière de sécurité.
Considérations de sécurité pour l'intégration de l'IA
Les organisations qui mettent en œuvre des technologies d'IA doivent prendre en compte plusieurs aspects de la sécurité :
- Modéliser la sécurité pour prévenir les attaques adverses qui manipulent le comportement de l'IA
- Protection de la confidentialité des données pour les données d'apprentissage et les données d'inférence
- Sécurité de la chaîne d'approvisionnement pour les cadres, les bibliothèques et les modèles pré-entraînés d'IA
- Contrôle des préjugés et de l'équité pour prévenir les résultats discriminatoires
- Exigences d'explicabilité pour la conformité et la responsabilité
Le rythme rapide des progrès de l'IA signifie que les pratiques de sécurité sont encore en cours de maturation. De nombreux experts suggèrent de traiter les systèmes d'IA avec une attention particulière lors des examens de sécurité et des exercices de modélisation des menaces.
Combler le fossé entre la sécurité et la direction de l'entreprise
L'un des défis persistants de la transformation numérique sécurisée est la déconnexion entre les équipes de sécurité et la direction de l'entreprise. Les dirigeants se concentrent sur la vitesse d'innovation, l'avantage concurrentiel et l'expérience client. Les professionnels de la sécurité mettent l'accent sur l'atténuation des risques, la conformité et la prévention des menaces.
Ces priorités ne sont pas intrinsèquement opposées, mais elles sont souvent communiquées dans des langues incompatibles.
Les responsables de la sécurité doivent formuler les discussions en termes commerciaux. Plutôt que de parler du nombre de vulnérabilités et du cycle des correctifs, les responsables de la sécurité traduisent les risques techniques en impacts commerciaux : perte de revenus due aux temps d'arrêt, atteinte à la réputation due aux violations, sanctions réglementaires dues à la non-conformité.
Quatre approches permettent de combler cette lacune :
- Quantifier le risque en termes financiers qui résonnent avec la prise de décision des dirigeants.
- Aligner les initiatives en matière de sécurité sur les objectifs de l'entreprise et les objectifs de transformation
- Démontrer que la sécurité est un facteur d'innovation plutôt qu'un obstacle
- Établir des indicateurs de performance clés en matière de sécurité que les chefs d'entreprise comprennent
Les organisations qui intègrent avec succès la sécurité dans la transformation numérique la considèrent comme une fonction stratégique de l'entreprise, et non comme une réflexion technique après coup. Les responsables de la sécurité participent à la planification de la transformation dès le début, en veillant à ce que la protection soit intégrée dans les nouveaux systèmes plutôt que d'être mise en place ultérieurement.
Mise en place de capacités de surveillance et de réaction en continu
Les contrôles de sécurité statiques ne peuvent pas suivre le rythme des environnements numériques dynamiques. Les entreprises ont besoin d'une surveillance continue qui s'adapte aux changements d'infrastructure, aux nouvelles menaces et à l'évolution des besoins de l'entreprise.
Selon le rapport SANS State of ICS/OT Security 2025, les lacunes en matière de visibilité représentent une faiblesse critique. Sans une surveillance complète de tous les systèmes - y compris les charges de travail dans le cloud, l'infrastructure sur site, les appareils IoT et la technologie opérationnelle - les équipes de sécurité fonctionnent partiellement à l'aveugle.
Un contrôle continu efficace nécessite
- Journalisation centralisée qui regroupe les données de tous les systèmes et services
- Détection automatisée des menaces à l'aide de l'analyse comportementale et de l'apprentissage automatique
- Alerte en temps réel avec priorisation intelligente pour réduire le bruit
- Des flux de travail intégrés qui accélèrent l'investigation et la remédiation
- Des mesures et des tableaux de bord qui fournissent une visibilité sur la posture de sécurité
L'objectif n'est pas seulement de détecter les menaces plus rapidement. Il s'agit de renforcer la résilience de l'organisation, c'est-à-dire sa capacité à résister aux attaques, à en minimiser l'impact et à se rétablir rapidement en cas d'incident.
| Capacité de sécurité | Approche réactive | Approche proactive |
|---|---|---|
| Détection des menaces | Balayage basé sur la signature | Analyse comportementale + renseignements sur les menaces |
| Réponse aux incidents | Enquête manuelle | Automatisation des playbooks et de l'orchestration |
| Gestion de la vulnérabilité | Balayage périodique | Évaluation continue et définition des priorités |
| Tests de sécurité | Tests de pénétration annuels | Validation continue + red teaming |
| Contrôle de conformité | Audits ponctuels | Vérification continue de la conformité |
Sécurité des tiers et de la chaîne d'approvisionnement
Les organisations modernes fonctionnent rarement de manière isolée. Elles intègrent des services provenant de fournisseurs de cloud, de fournisseurs SaaS, de partenaires API et de fournisseurs de technologie. Chaque point d'intégration représente une faiblesse potentielle en matière de sécurité.
Les attaques contre la chaîne d'approvisionnement sont de plus en plus sophistiquées. Les attaquants ciblent les fournisseurs les moins sécurisés comme points d'entrée dans les organisations les mieux protégées. Une fois dans l'environnement d'un partenaire de confiance, les attaquants peuvent pivoter vers leurs cibles ultimes.
La gestion des risques liés aux tiers nécessite :
- Évaluation de la sécurité des fournisseurs avant l'approbation de l'intégration
- Contrôle continu de la posture de sécurité des tiers
- Exigences contractuelles en matière de sécurité avec des responsabilités claires
- Coordination de la réponse aux incidents au-delà des frontières de l'organisation
- Segmentation pour limiter l'accès des tiers aux seuls systèmes nécessaires
Les organisations doivent également prendre en compte les implications de sécurité des dépendances open-source, en particulier dans les implémentations d'IA et d'apprentissage automatique où les modèles pré-entraînés et les cadres proviennent de sources externes.
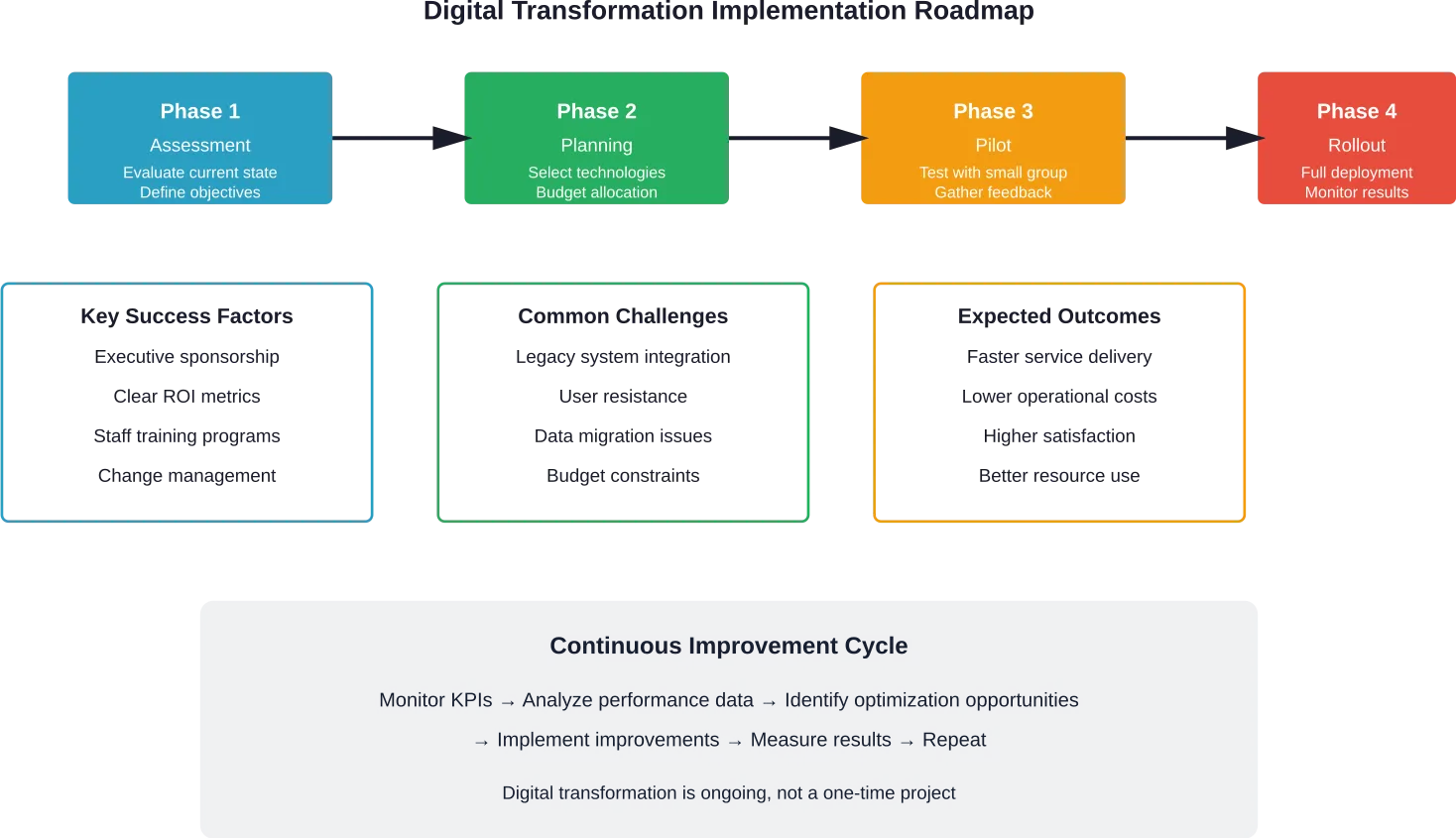
Étapes pratiques pour une transformation numérique sécurisée
Par où les organisations doivent-elles commencer ? La sécurité de la transformation numérique peut sembler écrasante, mais la diviser en étapes gérables rend les progrès réalisables.
Commencez par une évaluation. Comprendre la situation actuelle en matière de sécurité, identifier les initiatives de transformation en cours ou prévues, et déterminer où les lacunes en matière de sécurité pourraient apparaître. Utilisez des cadres tels que les normes NIST ou ISO pour structurer l'évaluation.
Établir des priorités en fonction des risques. Toutes les améliorations de la sécurité n'ont pas la même valeur. Concentrez-vous d'abord sur la protection des actifs critiques, sur les menaces les plus probables et sur les lacunes qui, si elles étaient exploitées, causeraient le plus de dommages à l'entreprise.
Intégrer la sécurité dans la planification de la transformation. Les équipes chargées de la sécurité devraient participer dès le départ aux révisions de l'architecture, à la sélection des fournisseurs et aux décisions de mise en œuvre. L'adaptation de la sécurité après le déploiement coûte plus cher et est moins efficace.
Investir dans la visibilité et la surveillance. Les entreprises ne peuvent pas protéger ce qu'elles ne peuvent pas voir. Une visibilité complète sur les environnements hybrides permet une détection plus rapide des menaces et une réponse plus efficace.
Sensibiliser l'ensemble de l'organisation à la sécurité. Les contrôles techniques n'ont qu'une portée limitée. Les employés doivent comprendre leur rôle dans le maintien de la sécurité, d'autant plus que les attaques de phishing et d'ingénierie sociale sont de plus en plus sophistiquées.
Tester en permanence. Des tests de sécurité réguliers - notamment des évaluations de la vulnérabilité, des tests de pénétration et des exercices de l'équipe rouge - permettent de vérifier que les contrôles fonctionnent comme prévu et d'identifier les faiblesses avant que les attaquants ne le fassent.
Questions fréquemment posées
- Qu'est-ce que la transformation numérique pour la sécurité ?
La transformation numérique pour la sécurité est l'intégration stratégique des principes, technologies et pratiques de cybersécurité tout au long des initiatives de modernisation organisationnelle. Elle implique la protection des données, des systèmes et des opérations à mesure que les entreprises adoptent l'infrastructure cloud, les technologies d'IA, les appareils IoT et les processus digital-first en utilisant des cadres tels que l'architecture zéro confiance et la surveillance continue.
- Pourquoi la sécurité est-elle importante dans la transformation numérique ?
La sécurité est essentielle car la transformation numérique élargit les surfaces d'attaque, introduit de nouvelles vulnérabilités et augmente la valeur et l'accessibilité des données de l'organisation. Sans intégration de la sécurité, les initiatives de transformation créent des risques qui peuvent conduire à des violations de données, des perturbations opérationnelles, des violations de la conformité et des pertes financières. Selon l'étude de SANS, plus d'une organisation sur cinq (21,5%) a déclaré avoir subi un incident de cybersécurité ayant entraîné une perturbation opérationnelle en 2025.
- Qu'est-ce que l'architecture de confiance zéro ?
L'architecture de confiance zéro est un modèle de sécurité qui part du principe que les réseaux sont déjà compromis et qui exige une vérification pour chaque demande d'accès, quelle qu'en soit l'origine. Basée sur le modèle de maturité de la confiance zéro de la CISA, elle applique l'accès au moindre privilège, vérifie explicitement en utilisant toutes les données disponibles, segmente les réseaux pour minimiser l'impact de la violation et surveille en permanence toutes les activités plutôt que de s'appuyer sur des défenses périmétriques.
- Comment la transformation de l'informatique en nuage affecte-t-elle la sécurité ?
La transformation de l'informatique en nuage déplace les responsabilités en matière de sécurité grâce à des modèles de responsabilité partagée dans lesquels les fournisseurs gèrent l'infrastructure physique tandis que les entreprises configurent et sécurisent leurs applications, leurs données et leurs contrôles d'accès. Elle nécessite de nouvelles approches de la gestion des identités, de la protection des données, du contrôle de la conformité et de la réponse aux incidents, adaptées aux environnements distribués et pilotés par des API, dans lesquels les contrôles traditionnels du périmètre ne s'appliquent pas.
- Quels sont les défis en matière de sécurité posés par l'IA ?
L'IA pose plusieurs problèmes de sécurité, notamment les attaques adverses qui manipulent le comportement des modèles, les risques pour la vie privée liés aux données d'entraînement et aux entrées d'inférence, les vulnérabilités de la chaîne d'approvisionnement dans les cadres et les modèles pré-entraînés, et la démocratisation des techniques d'attaque sophistiquées. Les organisations doivent également se pencher sur la surveillance des biais, les exigences en matière d'explicabilité et les implications en matière de sécurité d'une forte dépendance à l'égard de services d'IA tiers.
- Comment les équipes de sécurité peuvent-elles mieux travailler avec les chefs d'entreprise ?
Les équipes de sécurité peuvent améliorer la collaboration en traduisant les risques techniques en impacts commerciaux, en quantifiant les problèmes de sécurité en termes financiers, en alignant les initiatives de sécurité sur les objectifs de transformation et en démontrant comment la protection favorise l'innovation au lieu de la bloquer. Une communication efficace se concentre sur les résultats commerciaux tels que la protection des revenus, la préservation de la réputation et l'avantage concurrentiel plutôt que sur les mesures techniques.
- Quelles sont les priorités des organisations en matière de transformation sécurisée ?
Les organisations devraient privilégier une visibilité et une surveillance complètes des environnements hybrides, la mise en œuvre d'une architecture de confiance zéro, l'intégration de la sécurité dans la planification de la transformation dès le début, une priorisation basée sur les risques qui protège d'abord les actifs critiques, des tests de sécurité et une validation continus, et la sensibilisation à la sécurité de tous les employés qui interagissent avec les systèmes et les données numériques.
Aller de l'avant avec la transformation sécurisée
La transformation numérique n'est plus facultative. Les organisations qui ne se modernisent pas risquent de perdre leur compétitivité à mesure que les attentes des clients, les conditions du marché et les capacités technologiques évoluent.
Mais la transformation sans la sécurité est une recette pour le désastre. Les mêmes technologies qui permettent l'innovation des entreprises créent également des opportunités pour les adversaires. L'adoption du cloud, l'intégration de l'IA, le déploiement de l'IoT et le travail à distance élargissent tous la surface d'attaque que les équipes de sécurité doivent défendre.
La bonne nouvelle ? La sécurité n'a pas à ralentir la transformation. Lorsqu'elle est correctement intégrée dès le départ, la sécurité permet une innovation plus rapide et plus sûre en réduisant les risques et en renforçant la confiance des parties prenantes.
Les organisations qui considèrent la sécurité comme un élément fondamental de la transformation - et non comme une réflexion après coup - se positionnent pour saisir les opportunités numériques tout en protégeant les actifs, les données et les opérations qui assurent la viabilité de leur entreprise. Les cadres du NIST, de la CISA et de l'ISO fournissent des structures éprouvées pour l'élaboration de programmes de transformation sécurisés.
La question n'est pas de savoir s'il faut se transformer en toute sécurité. Il s'agit de savoir à quelle vitesse les entreprises peuvent faire évoluer leur dispositif de sécurité pour s'adapter au rythme de leurs ambitions numériques.
Commencez par évaluer les capacités actuelles, identifiez les priorités de transformation et établissez des partenariats de sécurité entre les équipes techniques et la direction de l'entreprise. La voie de la transformation numérique sécurisée commence par cette première étape intégrée.